Part 2 of 2: Identity, Trust, and Governance as the Control Plane Above CIA
The CIA triad protects data. It was never designed to govern the actors touching it. As infrastructure disappeared into abstraction, we kept using the ground-floor blueprint for a building that now has fifty stories.
In Part 1, I laid out the case that the CIA triad -- Confidentiality, Integrity, and Availability -- is incomplete. The evidence is overwhelming: 74% of attacks start with compromised identities. 79% of cyberattack detections are malware-free. 88% of web application breaches involve stolen credentials. The breaches aren't happening because encryption failed or integrity controls broke. They're happening because identity -- the question of who is making this request -- was never elevated to a foundational security principle.
The intuitive fix is to add Identity as a fourth pillar. CIA-I. And that would help.
But as I dug deeper, something else emerged. Every pillar of the CIA triad describes a property of data. Identity describes a property of actors. When you need to protect a fundamentally different kind of thing, you don't always need a wider foundation. Sometimes you need a second floor.
This is that argument. And it starts with a disappearing act.
The Disappearing Server#
Think about what happened to infrastructure over the last twenty-five years. Not as a technology story -- as a disappearing act.
Physical servers: you own everything#
In the beginning, security and infrastructure were the same conversation. You controlled the hardware, the operating system, the network, the application, the data. The CIA triad mapped perfectly to this world because the thing you were protecting -- the data -- lived on a thing you could touch. Firewalls at the perimeter. Encryption on the disk. Redundancy in the rack. Every security control had a physical address.
Virtual machines: the first split#
VMware changed the game in the late 1990s. Suddenly one physical server ran dozens of virtual ones. The security perimeter fractured. A single compromised hypervisor could expose hundreds of workloads. East-west traffic between VMs on the same host bypassed traditional network monitoring entirely.
But the bigger change was conceptual. For the first time, security responsibility split between layers. The hypervisor operator protected the physical infrastructure. The VM tenant protected the operating system and application. CIA still applied -- but you now had to ask: whose confidentiality? Whose integrity?
This was the seed of the shared responsibility model. And it was the first crack in the assumption that CIA alone was sufficient.
Containers: identity between services becomes critical#
Docker and Kubernetes took the abstraction further. Containers are ephemeral. They share the host kernel. They spin up and die in seconds. IP addresses are meaningless because they change with every deployment.
When IP-based identity became meaningless, the entire security model shifted. As GitGuardian reported from KubeCon 2025: "Trust is moving off the network and deeper into identity." Every service communicates via mutual TLS, both sides presenting certificates, both sides verifying. SPIFFE emerged to give workloads cryptographic identity. Open Policy Agent emerged to enforce fine-grained authorization.
The shift wasn't incremental. It was categorical: from "secure the host" to "secure the workload." And securing the workload meant knowing who the workload was.
Serverless: the server vanishes entirely#
With AWS Lambda, the developer writes a function. The cloud provider manages everything else -- the server, the operating system, the runtime, the scaling, the patching. The developer never sees a server. It doesn't exist in their mental model.
AWS's own documentation makes the security implication explicit: when a Lambda function executes, the platform issues temporary IAM credentials representing the function's assigned role. Those credentials determine what the function can access. When the function ends, the credentials expire.
The entire security surface has collapsed to one thing: identity and permissions.
AWS states it plainly in their shared responsibility model: "The more AWS abstracts away the inner workings of a service, the less responsibility the customer has." At the serverless layer, the customer's security responsibility reduces to: identity, permissions, data classification, and code logic. That's it. The infrastructure is someone else's problem.
AI agents: the human vanishes too#
If serverless abstracted the server away from the developer, agentic AI abstracts the developer away from the intent. The human expresses a goal. The AI agent writes the code, makes the API calls, spawns sub-agents, and orchestrates the workflow. The human doesn't touch the infrastructure. The human doesn't even touch the code.
ISACA's landmark 2025 article captured the inflection: "The IAM infrastructures that organizations rely upon today were built for human beings and fixed service accounts. They were not designed to manage autonomous AI systems that can reason about goals, make independent decisions, and dynamically adapt their actions."
Companies report between 1 and 17 AI agents per employee today. Each one authenticates hundreds of times per minute. Each one makes autonomous decisions at machine speed. Each one operates with delegated authority from a human sponsor. And increasingly, agents spawn sub-agents that inherit permissions the human never explicitly granted.
No one is monitoring the grandchildren.
The Pattern No One Named#
Step back and look at what happened across those five eras. There's a pattern, and it's not subtle.
| Era | What You Control | What You Don't | Primary Security Surface |
|---|---|---|---|
| Physical | Everything | Nothing | Infrastructure (firewalls, encryption, redundancy) |
| Virtual | OS, app, data | Hardware, hypervisor | Isolation + infrastructure |
| Container | App logic, configs | OS, kernel, host | Workload identity + supply chain |
| Serverless | Code, permissions | Runtime, OS, hardware, scaling | Identity and policy |
| Agentic AI | Intent, governance | Code, infra, API calls, sub-agents | Delegation, trust, accountability |
At every layer of abstraction, security responsibility migrated upward. Away from infrastructure. Toward identity, policy, and governance.
At the physical layer, CIA covered nearly 100% of the security surface. By the serverless layer, CIA covers maybe 30%. By the agentic layer, CIA addresses almost none of the novel risks.
It's not that confidentiality, integrity, and availability stopped mattering. They didn't. Data still needs to be encrypted. Integrity still needs to be maintained. Systems still need to be available. But these are now table-stakes protections handled largely by the cloud provider beneath you. They're the foundation -- and the critical security decisions have moved to a floor above.
Gartner found that over 99% of cloud security failures are the customer's fault -- due to misconfigurations and identity/policy errors, not infrastructure flaws. CrowdStrike's 2025 Global Threat Report found that 79% of cyberattack detections were malware-free: attackers are using credential abuse and identity-based techniques, not traditional exploits. The Verizon 2025 DBIR found 88% of basic web application breaches involved stolen credentials.
The data is screaming. The security problems have moved upstairs. The model hasn't followed.
Data Plane and Control Plane#
Here's the framing that makes the abstraction precise.
In computer networking, operations are divided into two planes. The data plane moves packets. The control plane decides where packets go. The data plane does the work. The control plane makes the decisions.
The CIA triad is the data plane of security. It describes the properties that must hold for information: confidential, intact, available. These are enforcement-level concerns. Encrypt this. Don't modify that. Keep these systems running.
But who decides what gets encrypted? Who determines which modification is authorized and which is an attack? Who defines which users should have access to which systems?
That's the control plane. And the control plane of security is identity.
This isn't a metaphor I invented. Gartner's 2024 report stated it formally: identity and access management has evolved into "the core control plane for cybersecurity." The World Economic Forum's Global Cybersecurity Outlook 2026 declared: "Whether human or non-human, identities have become the new control plane of modern cybersecurity." Surya Teja Avirneni published the foundational academic paper on arXiv in April 2025: "Identity Control Plane: The Unifying Layer for Zero Trust Infrastructure."
The language is converging because the reality already converged. Identity doesn't compete with CIA. It sits above CIA and governs it. The same way a networking control plane doesn't carry data -- it tells data where to go.
The Three Components of the Second Floor#
If CIA is the data plane -- the ground floor that protects information -- what sits above it?
The research converges on three components. Every major framework, standard, and industry report from 2024-2026 independently arrives at the same trio.
Identity: who or what is this?#
Identity is the primary component. It answers the question the CIA triad assumes is already solved: who or what is making this request, and can we verify that claim?
In the perimeter era, the answer was simple: they're inside the building. In 2026, the answer might be: an AI agent spawned by another AI agent, operating in a cloud environment the human sponsor has never seen, accessing data across three jurisdictions, carrying delegated authority inherited through a chain four levels deep.
CISA's Zero Trust Maturity Model places Identity as Pillar One -- before devices, networks, applications, or data. NIST 800-207 defines the key paradigm shift as "the change in focus from security controls based on segmentation and isolation using network parameters to identities." Microsoft's STRIDE threat model -- the standard threat classification used across the industry -- contains six threat categories. Three map to CIA properties. The other three -- Spoofing, Repudiation, and Elevation of Privilege -- all map to identity properties outside of CIA.
When Microsoft actually modeled threats, half the categories pointed to properties CIA doesn't cover. And every single one of those missing properties is about identity.
Jeffrey Nickle captured the distinction most sharply in his AAAA model: "CIA protects data; AAAA protects the actors." Authentication, Authorization, Accounting, Auditability -- every element is identity-centric.
Identity is the load-bearing wall of the second floor.
Trust: how much should we rely on this entity?#
Identity tells you who. Trust tells you how much.
An entity can be fully authenticated -- strong credentials, verified identity -- and still be untrustworthy. A legitimate employee account accessing sensitive financial data at 3 AM from an unfamiliar country is an identity concern. Whether to allow it is a trust concern.
Zero Trust's very name elevates trust to a first-class security concept. The framework didn't call itself "Zero Access" or "Zero Identity." It called itself "Zero Trust" -- implying trust is the fundamental currency being managed.
Gartner formalized this with CARTA (Continuous Adaptive Risk and Trust Assessment), which treats trust as a continuous, dynamic variable -- not a binary yes/no at the gate, but a constantly adjusting signal based on behavior, context, risk indicators, and environmental conditions. CISA's Zero Trust Maturity Model structures its five pillars around Identity, Devices, Networks, Applications, and Data -- but the cross-cutting capabilities that govern all pillars are: Visibility and Analytics, Automation and Orchestration, and Governance. These are trust-evaluation and trust-enforcement mechanisms.
In the agentic era, trust becomes even more critical. The World Economic Forum's 2026 report found that "the most common supply-chain risk is not malware -- it is inherited trust." When an agent delegates authority to a sub-agent, trust propagates through the chain. If any link is compromised, trust is compromised downstream.
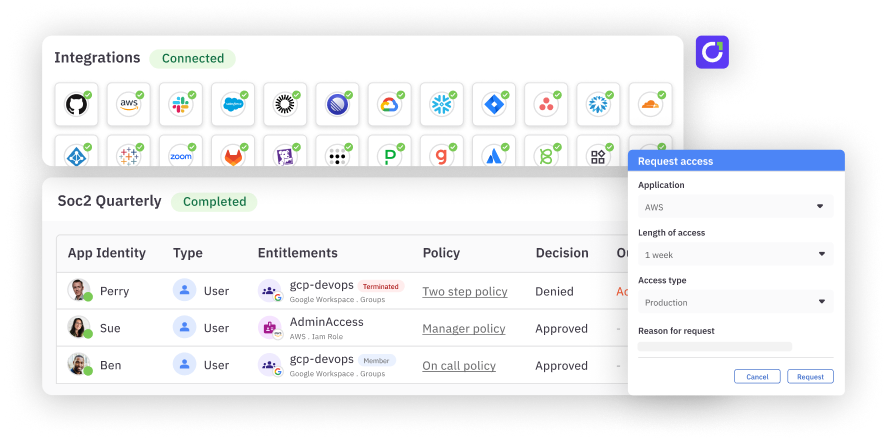
CyberArk published "Zero Trust for AI Agents: Delegation, Identity and Access Control." The ARIA framework (Agent Relationship-based Identity and Authorization) treats delegation relationships as explicit, trackable entities -- because trust in an agent system isn't just about authenticating the agent. It's about verifying the entire delegation chain from the original human through every intermediate agent to the one making the current request.
Trust is the dynamic evaluator on the second floor -- constantly adjusting, context-aware, never static.
Governance: by what rules, and who is accountable?#
Identity tells you who. Trust tells you how much. Governance tells you what the rules are, and who answers when things go wrong.
NIST Cybersecurity Framework 2.0, released in February 2024, made the most significant structural move in its history: it added GOVERN as a sixth core function and placed it at the center of the framework. Not at the edge. Not as an afterthought. At the center, informing all other functions.
The original five functions were Identify, Protect, Detect, Respond, Recover. Only "Protect" maps cleanly to the CIA triad. When NIST redesigned the framework for 2024, the missing piece wasn't another data-protection property. It was governance.
The EU AI Act, taking effect August 2026, makes governance non-optional for autonomous systems. Risk assessment, transparency, technical deployment controls, and human oversight design are all legally mandated. As one analysis stated: "Risk governance, transparency, and accountability are no longer optional -- they are central to being compliant."
Policy-as-code has emerged as the implementation mechanism. Organizations adopting it report 40-70% reduction in compliance costs while improving governance effectiveness. Cedar, OPA, and OpenFGA are authorization engines that make policies machine-readable, version-controlled, and executable at the speed agents operate.
But governance is more than policy. It's accountability. When an AI agent makes an autonomous decision that causes harm, who is responsible? The agent? The human who deployed it? The vendor who built it? 92% of agencies lack auditability for agentic decisions. Governance is the framework that answers this question before the question becomes a lawsuit.
Governance is the rule system on the second floor -- the policies, the accountability chains, the audit trails that constrain what identity and trust allow.
The Building, Not Just the Floor#
Here's the full picture.
┌─────────────────────────────────────────────────┐
│ CONTROL PLANE (Second Floor) │
│ │
│ IDENTITY + TRUST + GOVERNANCE │
│ (who) (how much) (by what rules)│
│ │
│ Governs the actors and their decisions │
├─────────────────────────────────────────────────┤
│ DATA PLANE (Ground Floor) │
│ │
│ CONFIDENTIALITY + INTEGRITY + AVAILABILITY │
│ (CIA Triad) │
│ │
│ Protects the information itself │
└─────────────────────────────────────────────────┘
The CIA triad remains the foundation. It doesn't go away. You still need confidentiality -- data must be protected from unauthorized access. You still need integrity -- data must not be tampered with. You still need availability -- systems must be operational.
But these are now the ground floor. The properties you need at the data level. The stuff the infrastructure largely handles beneath you.
The second floor -- Identity, Trust, and Governance -- is where the actual security decisions happen in 2026. Who is this entity? Should we trust it right now in this context? What policies constrain what it can do? And if something goes wrong, who is accountable?
The ground floor protects the what. The second floor governs the who.
Why a Second Floor, Not a Wider Foundation#
Some will argue this is just extending the CIA triad. Add Identity as a fourth pillar. Call it CIA-I. Stay on the same floor.
The evidence says otherwise, and the infrastructure analogy explains why.
Abstraction layers exist because they solve different problems#
When VMware introduced the hypervisor, nobody said "let's just add virtualization as another feature of the physical server." They recognized it was a fundamentally different layer -- an abstraction that sat above physical hardware and solved different problems. The hypervisor doesn't make the CPU faster. It decides which workload gets access to the CPU.
Identity doesn't make data more confidential. It decides which entity gets access to confidential data. That's a different layer of concern.
The shared responsibility model proves the layers are distinct#
AWS, Azure, and Google Cloud all document their shared responsibility models. As you move from IaaS to PaaS to SaaS, the customer's responsibility shrinks. At the SaaS level, the customer is responsible for exactly two things: identity/access management and data protection.
Read that again. At the highest abstraction layer, when all infrastructure is someone else's problem, the two remaining security concerns map exactly to the two floors: data protection (CIA) and identity/access (the second floor).
The cloud providers have been showing us the architecture for a decade. We just haven't drawn the diagram.
Extending the foundation doesn't fix the structural problem#
Donn Parker tried widening the foundation in 1998 with the Parkerian Hexad -- adding Possession, Authenticity, and Utility alongside the original three. Vladimir Jirasek tried it again in 2025 with the CIANA Pentad -- adding Non-repudiation and Authenticity. Both proposals widen the ground floor.
But notice what the additions are. Authenticity -- verifying that something comes from a genuine source. Non-repudiation -- proving that an actor performed an action. Possession -- controlling who holds the asset. Every extension points upward toward identity. Even when people try to widen the foundation, they end up reaching for the ceiling.
The Samonas and Coss counter-argument (2014) claims CIA is elastic enough to absorb all proposed extensions through "broader re-conceptualization." Technically true. You can run everything on bare metal. You can stretch the physical server to do what a hypervisor does. But the history of computing shows that abstraction layers exist because they make the system manageable -- not because the lower layer is incapable.
The same logic applies here. You can stretch CIA to cover identity concerns. Organizations have been trying for decades. The result is a 70% IAM implementation failure rate, 80% C-suite dissatisfaction, and 99% of service accounts over-permissioned. Stretching the foundation isn't working. It's time to build the second floor.
What the Second Floor Looks Like in Practice#
This isn't abstract theory. Each floor maps to concrete organizational decisions.
Ground floor (CIA) decisions#
These are the decisions security teams have been making for decades, and they remain essential:
- What encryption standard do we use for data at rest and in transit?
- How do we protect data integrity across distributed systems?
- What's our uptime SLA and disaster recovery plan?
- How do we classify data sensitivity?
These are solved problems in the sense that frameworks, tools, and best practices exist. They are well-funded, well-understood, and generally well-implemented. Not perfect -- but the failure modes are known and the solutions are mature.
Second floor (ITG) decisions#
These are the decisions that determine whether an organization gets breached in 2026:
Identity:
- What entity types exist in our environment? Humans, service accounts, AI agents, sub-agents, workloads?
- How do we issue, verify, and revoke identity for each type?
- What is the delegation chain from a human to the AI agents acting on their behalf?
- How do we handle identity for entities that didn't exist when we designed the system?
Trust:
- How do we continuously evaluate trust for every entity at every access decision?
- What behavioral baselines distinguish normal from anomalous?
- How does trust propagate through agent delegation chains?
- What triggers a trust score change, and how fast do we respond?
Governance:
- Are our policies machine-readable and enforceable at machine speed?
- Can we prove who did what across every entity type?
- How do we maintain compliance across 137 jurisdictions simultaneously?
- When an AI agent causes harm, who is accountable?
The organizations getting breached in 2026 generally have solid ground floors. Their data is encrypted. Their systems have integrity controls. Their infrastructure is available. The breaches happen on the second floor -- compromised identities, misplaced trust, governance gaps.
The Counter-Argument and Why It Fails#
The strongest objection is: "Identity, Trust, and Governance have always been implicit in the CIA triad. Confidentiality requires knowing who is authorized. Integrity requires trusting the source. Availability requires governing access. You don't need a new layer -- you need to implement the existing one better."
This argument is structurally identical to every argument against abstraction layers in computing history.
"You don't need virtual machines -- you just need to manage your physical servers better."
"You don't need containers -- you just need to configure your VMs properly."
"You don't need Kubernetes -- you just need to orchestrate your containers manually."
Each of these was technically true. And each was practically wrong. The abstraction layer won -- not because the lower layer couldn't do the job, but because the problem had grown beyond what the lower layer's mental model could manage.
CIA's mental model is: protect the data. That model was sufficient when the data lived on servers you controlled, accessed by people you knew, over networks you owned. It is not sufficient when the data lives everywhere, accessed by entities that may not be human, over networks that are someone else's infrastructure, governed by regulations that conflict across jurisdictions.
The problem outgrew the model. The model needs a second floor.
The Industry Is Already Building It#
The money tells the story.
Palo Alto Networks acquired CyberArk for $25 billion. Not for encryption capabilities. For identity. CrowdStrike acquired SGNL for $740 million -- a company whose sole product is continuous access evaluation. Google acquired Wiz for $32 billion. CyberArk acquired Venafi for $1.54 billion. Non-human identity startups raised over $400 million in 2025 alone.
Gartner predicts 70% of companies will prefer converged IAM platforms by 2026 -- not adding identity to their existing security stack, but making identity the platform that unifies the stack.
NIST put GOVERN at the center of CSF 2.0.
CISA put Identity as Pillar One of Zero Trust.
The EU mandated governance for autonomous systems in the AI Act.
Microsoft, in January 2026, recommended "unifying the identity and network access layers" through a single policy engine. They're literally building the second floor.
Descope raised $35 million to build an "Agentic Identity Control Plane." The product name says it all: identity, for agents, as a control plane. Not a feature within the CIA framework. A plane above it.
The Shared Signals Framework, CAEP, and SSF specifications approved by the OpenID Foundation in September 2025 are the plumbing of the second floor -- real-time signal propagation that lets Identity, Trust, and Governance operate at machine speed across every system simultaneously.
The industry isn't debating whether to build the second floor. It's debating who gets to be the general contractor.
What This Means for Security Leaders#
If your security strategy is organized entirely around the CIA triad -- confidentiality, integrity, availability -- you're maintaining the ground floor of a building where the tenants have moved upstairs.
Recognize the two floors. The CIA triad isn't wrong. It's incomplete. Your security architecture needs both a data plane (CIA) and a control plane (Identity, Trust, Governance). Budget, staff, and executive attention should reflect both.
Audit your second floor. Most organizations have solid ground floors. The questions that reveal second-floor gaps: How many entity types do we govern? What's our non-human identity ratio? Do AI agents have managed lifecycles? Can we trace delegation chains? Are policies machine-readable? How fast can we revoke access?
Staff the control plane. When Gartner says 70% of IAM implementations fail, they're describing organizations trying to build second-floor capabilities with ground-floor tools and ground-floor thinking. Identity, Trust, and Governance need dedicated leadership, dedicated investment, and dedicated measurement -- not a checkbox under the CISO's compliance obligations.
Match your tempo to your fastest entity. If AI agents make decisions at machine speed and your governance operates at quarterly-review speed, you're conducting yesterday's orchestra. Continuous authorization, real-time trust scoring, policy-as-code, and event-triggered governance aren't premium features. They're baseline requirements for the second floor.
Design for what's coming. The entity types that will exist in two years haven't been invented yet. Composable identity architecture -- authentication-as-a-service, authorization-as-a-service, governance-as-a-service -- is how you build a second floor that can absorb new tenants without structural renovation.
The View from the Second Floor#
For fifty years, the CIA triad has been the foundational model of information security. It will remain foundational. Data still needs confidentiality, integrity, and availability. These properties don't expire.
But the security problems of 2026 aren't about data properties. They're about actor properties. Who is this entity? Should we trust it? What rules constrain it? Who is accountable for what it does?
These questions aren't CIA's questions. They never were. They're the questions of a layer above -- a control plane that governs the data plane, the way a hypervisor governs physical hardware, the way Kubernetes governs containers, the way an operating system governs the CPU.
We kept the same ground-floor blueprint as we built fifty stories of abstraction above it. The CIA triad still holds the foundation. But the decisions that determine whether you get breached -- the identity of the entity, the trust you place in it, the governance that constrains it -- those happen on the second floor.
It's time to draw the rest of the building.
This is Part 2 of a two-part series. Part 1: The CIA Triad Was Built for a World That No Longer Exists makes the case that the foundational model of cybersecurity is incomplete.