Today, we're announcing the C1 Headless Identity Infrastructure.
We've never had a shortage of identity tools, yet somehow we've always had a shortage of outcomes. And now, agents and the need for customization are bringing us to a tipping point. Agents need programmatic interfaces for requesting permissions, creating other agents, assuming digital identity, grabbing scoped tokens and more. Customers also want the ability to integrate and customize their identity experiences through their organization. What's held us back: technology. Legacy products with no or incomplete APIs and no standardized identity graph that understand relationships, permissions, and access throughout your organization.
If you're an IT leader, you feel this daily: engineering cycles spent integrating identity tools that each solve a piece of the puzzle. Count the categories: IGA. PAM. Vault. AuthZ. NHI. Agent gateway. Each one solves its own slice and knows almost nothing about the others. The result is a patchwork, and you're the one holding it together.
Headless infrastructure matters because agents don't use consoles. They have no eyeballs, they do not click, and they don't file helpdesk tickets. If your identity infrastructure requires a human at a screen, it cannot govern what's coming.
Key capabilities of the C1 Headless Identity Infrastructure#
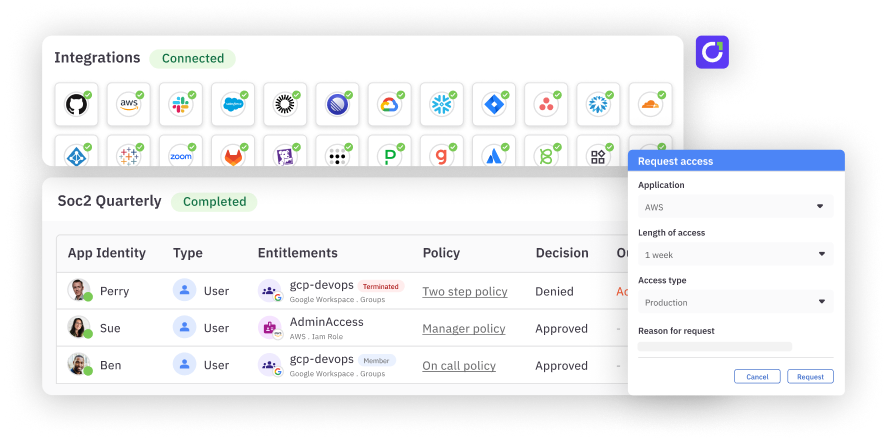
One identity graph. Every human, service account, workload, AI agent, role, entitlement, credential, and resource — across every IdP, SaaS app, cloud, and on-prem system — connected in a single graph with effective permissions computed in real time.
API-first everything, MCP and CLI for agents. Every capability ships callable as an API, an MCP tool, a CLI command, or an SDK. C1's MCP server exposes the primitives agents need — credential access, authorization checks, governed access requests — as self-describing tools for Claude Code, Cursor, Codex, Windsurf, and custom agents.
Inline authorization for any request. Authorization evaluated in real time, at the point of action. A policy decision point exposed as an API, with fine-grained enforcement against the live identity graph. Same evaluation whether the request comes from Slack, an MCP tool call, a workload, or the UI.
Continuous governance and defensible audit. Always-on controls, not quarterly campaigns. Every authorization decision, credential issuance, and policy outcome captured with full context — subject, actor, delegation chain, purpose, resource, policy, outcome.
Open connector fabric. C1's open source connector framework integrates IdPs, directories, SaaS applications, cloud infrastructure, and on-prem systems. Connectors run hosted or self-hosted, and credentials never leave the customer's environment.
The result: agents ship governed on day one. Access happens inline, not after a ticket. Audit becomes a query. Identity accelerates the work instead of slowing it down.
The road here, and what's ahead#
We started by making identity governance fast and frictionless for the modern workforce. Access requests in Slack, reviews that close in hours instead of weeks, policies that enforce themselves. We built the open connector fabric so any app could be plugged in.
Earlier this year, we launched AI Access Management to govern agent identities across Claude, OpenAI, and Cursor. AIAM works because C1 was already API-native and graph-driven. It extended our governance to a new class of identity.
The pattern is established: when a platform decouples logic from presentation, the experience layer multiplies and the ecosystem accelerates. Content figured this out around 2014. Commerce followed in 2018. Salesforce just made the same move with CRM, calling Headless 360 the most significant architectural change in their 27-year history. Identity is next. And the stakes are higher, because identity is the control layer for everything else.
EU AI Act enforcement begins August 2026. If you cannot trace every agent action — including credential and authorization events — back to a human sponsor, with full agent-to-human provenance, you will fail that audit. Compliance requires API-native delegation and provenance, not screenshots from six consoles.
The enterprises that win this era will not be the ones with the most agents. They will be the ones whose identity infrastructure was built for what's coming. We've been building it from the start.
If you want to learn more, book a demo.