Confidentiality, Integrity, and Availability assumed someone was guarding the door. In 2026, there is no door.
In 1973, a computer scientist at the RAND Corporation published a paper that would quietly shape the next fifty years of cybersecurity thinking. The Bell-LaPadula model formalized how to protect classified information on military computer systems. It focused on one thing: confidentiality. Who can read what.
Four years later, Kenneth Biba tackled the mirror problem: integrity. Who can modify what. In 1987, David Clark and David Wilson extended integrity to commercial environments with well-formed transactions and separation of duties.
From these roots grew the CIA triad -- Confidentiality, Integrity, and Availability -- the foundational model that every cybersecurity professional learns on day one, that every framework references, that every certification exam tests.
It was a brilliant framework. For its era.
The CIA triad was designed for a world of mainframes and terminals, wires and firewalls, web servers behind DMZs. A world where you knew which building the computer was in, which network it was on, and which human was sitting at the keyboard. A world where "security" meant protecting data at rest and in transit across networks with clear borders.
That world is gone. And the framework built for it is showing its age in ways that are getting people breached.
The World the CIA Triad Was Built For#
Think about what security looked like when these models were formalized.
Computers lived in rooms. Networks had edges. You could draw a line around your infrastructure and call everything inside "trusted" and everything outside "untrusted." Firewalls sat at the boundary. Intrusion detection systems watched the wires. Access control lists governed who could reach which server.
In this world, the CIA triad made perfect sense.
Confidentiality meant encrypting data and controlling access so unauthorized people couldn't read it. The tools: firewalls, encryption, access control lists.
Integrity meant ensuring data wasn't tampered with in transit or at rest. The tools: checksums, digital signatures, write protections.
Availability meant keeping systems running so authorized users could reach them. The tools: redundancy, backups, failover.
Notice what's implicit in all three: someone already knows who's asking. The triad assumes identity is solved. It assumes you've already determined who the user is, whether they're authorized, and what they're allowed to do. It treats identity as a precondition -- a problem handled upstream, before confidentiality, integrity, and availability even come into play.
When the user was a person sitting at a terminal in a secure building, that assumption held.
It doesn't hold anymore.
Five Things That Killed the Perimeter#
The world the CIA triad was built for didn't die overnight. It eroded in five waves, each one making identity more central and perimeter defenses less relevant.
Cloud blew up the boundary#
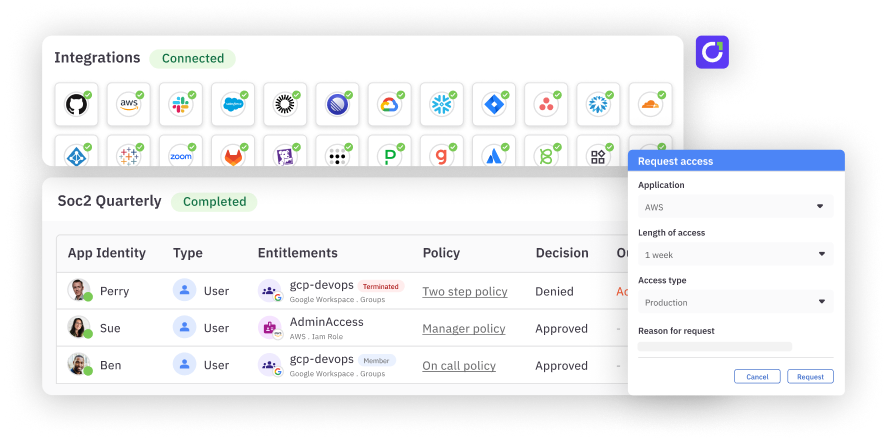
When your data lives in AWS, your applications run on Azure, your CRM is Salesforce, and your email is Google Workspace, there is no perimeter to defend. 86% of enterprises run multi-cloud strategies. Only 9% are fully cloud-based for identity. Most run three or more public clouds, each with its own identity subsystem.
The firewall that once defined "inside" and "outside" now protects an empty building. The data left years ago.
SaaS made everyone an outsider#
The average enterprise uses hundreds of SaaS applications. Every one of them lives outside your network. Every one of them requires its own authentication. Every one of them holds your data on someone else's infrastructure.
In this model, every user -- including your own employees -- accesses your systems from "outside." The concept of an insider network becomes meaningless. The only thing that distinguishes an authorized user from an attacker is identity.
APIs replaced humans#
Modern applications don't have users sitting at keyboards. They have APIs talking to APIs, services calling services, microservices authenticating to microservices -- thousands of times per second. When no human is in the loop, the traditional CIA question of "is this data protected from unauthorized access" becomes "does this service have a verifiable identity and the right authorization for this specific request at this specific moment."
SPIFFE emerged to give workloads cryptographic identity. OAuth evolved from user authorization to machine-to-machine authentication. The entire security model shifted from "protect the network" to "verify the identity."
Remote work dissolved the last walls#
When COVID sent the workforce home, the VPN became the new perimeter -- and immediately proved inadequate. The distinction between "on the corporate network" and "off the corporate network" collapsed. Zero trust -- John Kindervag's 2010 concept that "never trust, always verify" should replace perimeter trust -- went from academic idea to executive mandate.
NIST codified it in Special Publication 800-207: "A key paradigm shift in zero trust architectures is the change in focus from security controls based on segmentation and isolation using network parameters to identities." Every access decision, per-request, based on identity, posture, and context.
The perimeter didn't move. It disappeared. And identity was the only thing left standing.
AI agents created identities that aren't human#
This is the one that breaks everything.
Companies report between 1 and 17 AI agents per employee today. Forty percent of enterprise applications will embed task-specific agents by end of 2026. These agents authenticate hundreds of times per minute, make autonomous decisions at machine speed, and operate with delegated authority from human sponsors. They spawn sub-agents. Those sub-agents inherit permissions. Non-human identities now outnumber humans 144 to 1.
68% of organizations lack identity security controls for their AI systems. 97% of non-human identities have excessive privileges. 78% of organizations lack formal policies for even creating or removing AI identities.
The CIA triad was built for a world where "who's asking" was a person at a keyboard. Now "who's asking" might be an AI agent spawned by another AI agent, operating in a cloud environment the human sponsor has never seen, accessing data across jurisdictions the governance system doesn't cover.
Confidentiality, integrity, and availability still matter. But they're all downstream of a question the triad never learned to ask: who -- or what -- is this, and should it exist?
The Evidence: Identity Is the Primary Attack Surface#
If identity were just a supporting player in the CIA model, you'd expect most breaches to exploit failures in confidentiality (encryption broken), integrity (data tampered with), or availability (systems taken down). That's not what the data shows.
The numbers#
74% of attacks investigated in Q3 2025 were tied to compromised identities. Not broken encryption. Not tampered data. Not DDoS attacks. Compromised identities.
Microsoft reported that password-based attacks accounted for over 99% of the 600 million daily identity attacks it observed in 2024. The CrowdStrike 2025 Global Threat Report found that 79% of cyberattack detections were malware-free -- adversaries are using credential abuse and identity-based techniques, not traditional exploits. Access broker markets -- criminal marketplaces selling stolen credentials -- grew 50% year-over-year. The fastest recorded breakout time after credential compromise was 51 seconds.
The Verizon 2025 DBIR found 88% of basic web application breaches involved stolen credentials. Push Security analyzed 30 publicly confirmed breaches in 2024 and found 73% stemmed from compromised credentials. Microsoft detects 39,000 session token attacks per day. IBM's 2024 Cost of a Data Breach report found credential-based breaches cost $4.81 million on average and take 292 days to detect -- the longest of any attack vector.
The Identity Defined Security Alliance has tracked this trajectory for years: 79% of organizations experienced identity-related breaches in 2020. By 2022, it was 84%. By 2024, 90% -- with 84% reporting direct business impact.
The data isn't ambiguous. Credentials are the dominant initial access vector. Not network exploitation. Not zero-days. Credentials.
The breaches that prove it#
Microsoft Midnight Blizzard (January 2024). Russian state actors used a password spray attack against a legacy test tenant that lacked MFA. One compromised non-production account gave them access to senior leadership email, cybersecurity team communications, and eventually source code repositories. Microsoft's network security was world-class. Their firewalls were fine. Their encryption was fine. The identity was the failure.
Change Healthcare (February 2024). Stolen credentials used against Citrix remote access without MFA. UnitedHealth Group CEO Andrew Witty testified to Congress that the credential was not protected with MFA. The result: 192.7 million Americans affected -- the largest healthcare data breach in US history. Payment processing and insurance claims disrupted nationwide. A $22 million ransom paid. Total financial impact: $872 million. One credential. No MFA. Nearly 200 million people exposed.
Snowflake (April-June 2024). Credentials harvested from infostealer malware -- some dating back to 2020 -- were used against 165 organizations whose Snowflake environments lacked MFA. Hundreds of millions of customer records exposed across AT&T, Ticketmaster, Santander, and others. Snowflake's platform wasn't breached. The customers' data wasn't tampered with on disk. The identities were stolen, and everything else fell.
Okta (October 2023). An employee stored company credentials in a personal Google account. That credential was used to access Okta's support system, which contained HAR files with session tokens from 134 customers. Five customers had their active sessions hijacked, including BeyondTrust, 1Password, and Cloudflare. The identity provider's own identity was the vulnerability.
PowerSchool (2024). A single maintenance account without MFA. 72 million records exposed. One identity. One missing control.
In every case, the traditional CIA pillars were intact. Data was encrypted. Systems had integrity controls. Infrastructure was available. The identity was the breach.
Why "Identity Enables CIA" Isn't Enough#
The standard defense goes like this: Identity is already part of the CIA triad. It's the mechanism that enables confidentiality, integrity, and availability. You don't need a fourth pillar -- you just need to implement the existing three properly.
This argument is wrong. And the evidence shows why.
The servant problem#
When identity is treated as a servant of the three pillars -- a mechanism rather than a principle -- it gets implemented as an afterthought. Security teams design for confidentiality (encrypt the data), integrity (protect the data from modification), and availability (keep the systems running). Then they bolt on identity controls to support those goals.
This is exactly how the breaches above happened. Organizations had strong encryption (confidentiality). They had data integrity controls. They had redundancy and uptime (availability). What they didn't have was identity treated as a first-class security concern -- MFA everywhere, credential hygiene, continuous verification, identity lifecycle management.
When identity is subordinate to CIA, it gets budget, attention, and rigor proportional to its perceived status: a tool, not a foundation. And tools get shortcuts.
The implementation gap proves the hierarchy is wrong#
The security industry has a phrase for this: "70% of IAM implementations fail to meet expectations." More than half fail the first time. 81% of employees bypass security measures. 80% of C-suite leaders believe IAM delivers insufficient value. 99% of service accounts are over-permissioned. Only 2% of granted permissions are actually used.
If identity were truly a first-class principle in the CIA model, these numbers wouldn't exist. Organizations invest heavily in confidentiality (encryption is table stakes), integrity (compliance mandates it), and availability (downtime costs money). They underinvest in identity because the framework tells them it's a supporting capability, not a core principle.
The framework created the blind spot. The breaches exploited it.
The "we just need to implement it better" fallacy#
Some argue that the CIA triad's concepts are sufficient -- organizations just fail to implement them. As one security writer put it: "The CIA Triad isn't dead -- we just never actually implemented it."
But this misses the point. A framework's job is to direct attention and resources. If fifty years of security practice have consistently underinvested in identity relative to confidentiality, integrity, and availability, that's not an implementation failure. That's a framework failure. The model doesn't tell practitioners that identity is equally important. And so they don't treat it that way.
If you have to argue that identity is "implicit" in the CIA triad, it means the framework isn't doing its job of making identity explicit.
The Industry Already Knows#
Look at where the money is going.
Palo Alto Networks acquired CyberArk for $25 billion. CEO Nikesh Arora stated: "The time is now to re-shape the $29 billion Identity Security category and lead from the front." He described identity security as "a core pillar" of the company's platform strategy.
CrowdStrike acquired SGNL for $740 million -- a company whose sole product is continuous access evaluation for identity. Google acquired Wiz for $32 billion. CyberArk acquired Venafi for $1.54 billion. Non-human identity startups raised over $400 million in 2025 alone.
The identity security market is projected to grow from $29 billion to $56 billion by 2029.
Gartner VP Analyst Felix Gaehtgens put it plainly: "Moving identity to the centre of cyber security is key. It is the control plane and foundation of cyber security -- this is where focus needs to be." Gartner predicts 70% of companies will prefer converged IAM platforms that unify identity governance, access management, and privileged access. Not separate tools. Unified platforms.
The US federal government has already made the call. OMB Memorandum M-22-09 -- the Federal Zero Trust Strategy -- identified five pillars of zero trust, with Identity as Pillar One. CISA's Zero Trust Maturity Model places identity first among its five pillars. When the federal government architects security for the future, identity comes before devices, networks, applications, and data.
The Shared Signals Framework, CAEP, SPIFFE, WIMSE, and OAuth 2.1 represent identity becoming protocol-level infrastructure -- the same way TCP/IP became networking infrastructure. You don't think about TCP/IP as a tool that serves other goals. It's a foundation. Identity is on the same trajectory.
Others Are Already Arguing for Change#
The security community is waking up.
Vladimir Jirasek, CEO of Foresight Cyber, proposed expanding the CIA triad to a "CIANA pentad" in January 2025 -- adding Authenticity (verifying that communications come from genuine sources) and Non-repudiation (proving an actor performed an action). Both are fundamentally identity properties.
CSO Online published "The CIA triad is dead -- stop using a Cold War relic to fight 21st century threats." Haden Grey argued "The CIA Triad Isn't Dead -- It's Just Not Enough," proposing a three-layer model that adds Authenticity, Accountability, and Resilience as core properties alongside CIA. Again -- authenticity and accountability are identity.
The Parkerian Hexad, proposed by Donn Parker in 1998, already added Possession, Authenticity, and Utility to the traditional three. Germany's Federal Office for Information Security (BSI) already treats authenticity as a peer of C, I, and A in its national security framework.
At the 2020 RSA Conference, Sounil Yu (now CISO of JupiterOne and creator of the Cyber Defense Matrix) proposed the DIE triad -- Distributed, Immutable, Ephemeral -- arguing that if data is ephemeral, confidentiality matters less; if immutable, integrity is automatic; if distributed, availability is inherent. Jeffrey Nickle proposed the AAAA model -- Authentication, Authorization, Accounting, Auditability -- arguing that "CIA protects data; AAAA protects the actors."
Every serious proposal to expand or replace the CIA triad adds properties that are, at their core, identity properties. Authenticity is identity. Accountability is identity. Non-repudiation is identity. Authentication and authorization are identity. The community keeps arriving at the same destination through different paths.
The Obvious Answer: Add Identity as a Fourth Pillar#
The intuitive response to everything above is straightforward: add Identity as a fourth pillar. Call it CIA-I. Problem solved.
And the logic holds -- up to a point.
Confidentiality answers: Is the data protected from unauthorized access? But "unauthorized" requires knowing who's authorized. Without identity, confidentiality is a locked door with no way to check keys.
Integrity answers: Has the data been modified by someone unauthorized? But "unauthorized modification" requires knowing who modified it and whether they were allowed to. Without identity, integrity is a tamper seal that can't distinguish the owner from the thief.
Availability answers: Can authorized users access the system? But "authorized users" requires knowing who they are. Without identity, availability is an open door that can't tell friend from stranger.
Identity answers the question the other three depend on: Who or what is this entity, can we verify that claim, and what are they authorized to do right now in this context?
If identity were elevated to a foundational pillar, it would get its own budget line, its own risk assessment, its own incident response playbook. It would cover every entity type -- not just humans with passwords, but AI agents with delegated authority, sub-agents with inherited permissions, workloads with SPIFFE identities. Every entity that can access a system would need a governed identity lifecycle.
This is a meaningful improvement over the status quo. It would direct attention and resources where the breaches actually happen.
But is adding a pillar enough?
The Deeper Question#
Here's what nagged at me as I looked at the evidence.
Every pillar of the CIA triad describes a property of data. Confidentiality is a data property. Integrity is a data property. Availability is a data property. The framework's job is to protect information.
Identity is not a property of data. Identity is a property of actors. It answers a fundamentally different kind of question -- not "what should be true about this information?" but "who is touching this information, and should they be?"
When you add a fundamentally different kind of thing to an existing model, you don't always get a better model. Sometimes you get a signal that you need a different layer.
Think about it in infrastructure terms. When the computing world needed to run multiple operating systems on a single physical server, nobody added "virtualization" as a fourth property of the CPU alongside clock speed, cache size, and core count. They built a hypervisor -- a new layer that sat above the physical hardware and governed how it was used.
The CIA triad protects data. Identity governs who touches data. These might not be the same layer.
And if that's true, then the fix isn't adding a fourth pillar to the existing foundation. It's building a second floor.
The evidence suggests that identity isn't alone up there. The same research that points to identity as a missing element also points to trust and governance as co-equal concerns -- concepts that, like identity, describe properties of actors and decisions rather than properties of data.
But that's a bigger argument. One that requires tracing how security models have evolved alongside the infrastructure abstraction stack -- from physical servers to VMs to containers to serverless to agents -- and what that evolution reveals about where the real security decisions happen in 2026.
That's Part 2.