Shadow IT is a pressing—and rapidly growing—concern for today’s IT and security teams. In 2022, 41% of employees used technology outside of IT’s view, and Gartner predicts that percentage will rise to 75% by 2027. Shadow apps—SaaS applications that can be easily signed up for by employees using a work email address—present a particular security threat. Because these apps are being logged into and used without IT’s authorization, they do not receive the same scrutiny for potential risks as sanctioned apps, and policies defining who should have access to them, and how much access, cannot be enforced. Shadow apps fly under the radar, extending an organization’s attack surface area and putting sensitive company and customer data at risk.
Today C1 is excited to announce the addition of shadow app detection, tracking, and management capabilities to its core platform. This new functionality expands C1’s commitment to giving customers complete visibility into their access environment by enabling customers to view not only known applications but also those being used in the shadows. C1 customers will now be able to identify and monitor logins to unauthorized apps and, if they choose, bring those apps under full management in the platform.
View and manage shadow app activity directly in C1#
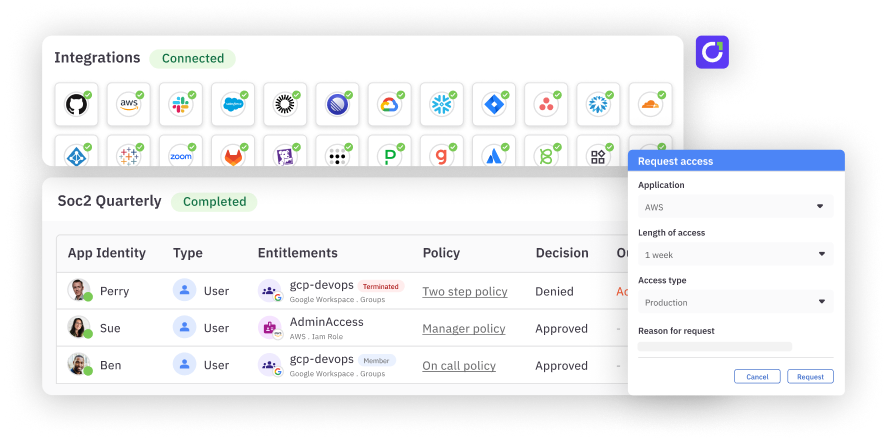
When an employee uses their IdP credentials to log into an unauthorized app, that activity will be logged in C1. Newly discovered shadow apps will be listed on the shadow apps page, and customers will be able to view subsequent employee login activity as it occurs.

If a customer wants to apply access controls to a shadow app, they can bring the app under management in C1 in a few clicks—they simply opt to authorize the app and assign it an owner. Once authorized, the app is added to the customer’s list of applications in C1 and can be managed like any other app.

Customers can also choose to ignore shadow apps that aren’t of current concern. Ignoring a shadow app removes it from the active list of tracked shadow apps, but C1 will continue to log the app’s usage activity, and the app can be un-ignored and brought under management at any time.

C1 currently detects shadow app logins from Google Workspace and Microsoft Entra ID.
A security-first approach to SaaS management#
Visibility into shadow app usage and the ability to quickly enforce access controls is a critical security win for IT and security teams struggling to stay on top of SaaS sprawl. Shadow app detection also allows teams to more effectively manage app licenses and costs through a better understanding of how apps are being used and the application of access controls that ultimately improve efficiency and reduce spend—all while increasing overall security.
C1’s shadow app capabilities are generally available today. Check out www.conductorone.com/solutions/shadow-it or book a demo with our team to learn more.