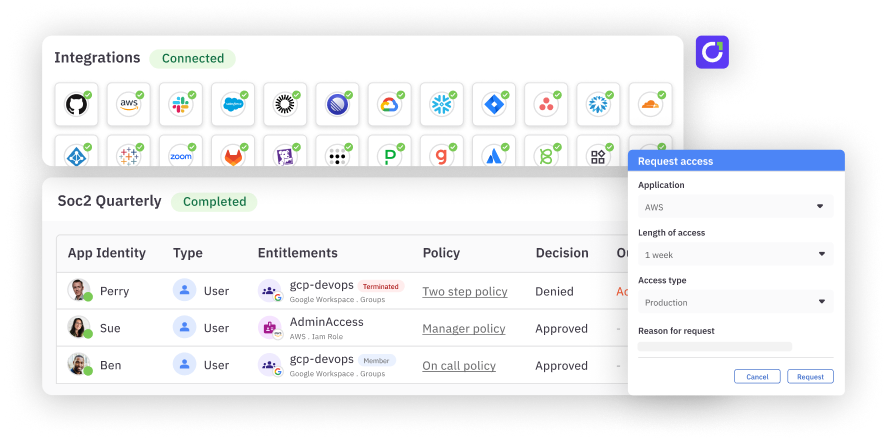
Identity data rarely lives in a single system. Job titles, managers, emails, and identifiers are often spread across multiple apps, and they’re not always consistent. Super Directory gives you precise control over how those attributes are sourced and how users are matched across systems.
Mapping attributes across multiple apps#
C1 allows you to map attribute values from different apps into a single user profile. For example, you might pull a job title from one app and a manager relationship from another.
With Super Directory, two tools let you decide exactly where those values come from.
Fallback mappings#
Fallback mappings allow you to define a clear order of precedence for attribute sources.
A common scenario is handling full-time employees and contractors. You might store full-time employees in one app and contractors in another. Both systems may contain a job title, but for any individual user, you do not always know which system holds that value.
With a fallback mapping, C1 will first check the full-time employee app for a job title. If that value does not exist, it will fall back to the contractors app and pull the job title from there.
This ensures that each user’s attribute is populated from the appropriate source without manual intervention.
CEL expressions#
CEL expressions are custom scripts you can write to populate an attribute with exactly the value you want. They give you flexibility to construct, transform, or derive attribute values during mapping.
CEL expressions can be used anywhere more advanced logic is required, especially when values need to be generated rather than copied directly from an app.
Advanced user matching in C1#
C1 automatically maps app users to users in C1 using several identifiers:
- Primary email
- Additional emails provided by connectors
- Username and additional usernames
- Display name, when BroadMatch is enabled
- Employee ID
In many environments, these automatic mappings are sufficient, but some ecosystems require additional configuration. ** ** One common issue often appears in Microsoft environments. Users often have emails ending in @corp.onmicrosoft.com, while their primary email may be @corp.com. These values do not directly match and can prevent users from being mapped correctly.
To address this, you can configure an attribute mapping for additional emails in your directory settings.
Using a CEL expression, you can take subject.email, split it on the @ symbol, and append @corp.onmicrosoft.com to the username portion. By selecting the first index of the split result, you preserve the username and construct a new additional email.
That email is then added to the user’s additional emails list in C1. When C1 matches users to the Microsoft app, it recognizes the new email and maps the app user correctly.
Precise control over identity data#
Attribute mapping in Super Directory gives you direct control over how attributes are sourced and how users are matched. Fallback mappings let you define where data should come from, and CEL expressions let you handle edge cases that automatic matching cannot resolve.
Together, these tools help ensure user data is accurate, complete, and consistently mapped across your environment.
Want to see it in action? Book a demo.