For a long time, identity systems operated on a simple premise: if you can prove who you are, you get access.
That model made sense when work was predictable, roles changed slowly, and access decisions could be made ahead of time. But that world doesn't exist anymore. Devices get compromised mid-session. Credentials are exposed. Service accounts sprawl. And now, AI agents are acting autonomously — calling APIs, making decisions, and interacting with systems at a scale that dwarfs human activity.
In this environment, the question is no longer just who an identity is. It's "Should this identity have access right now?"
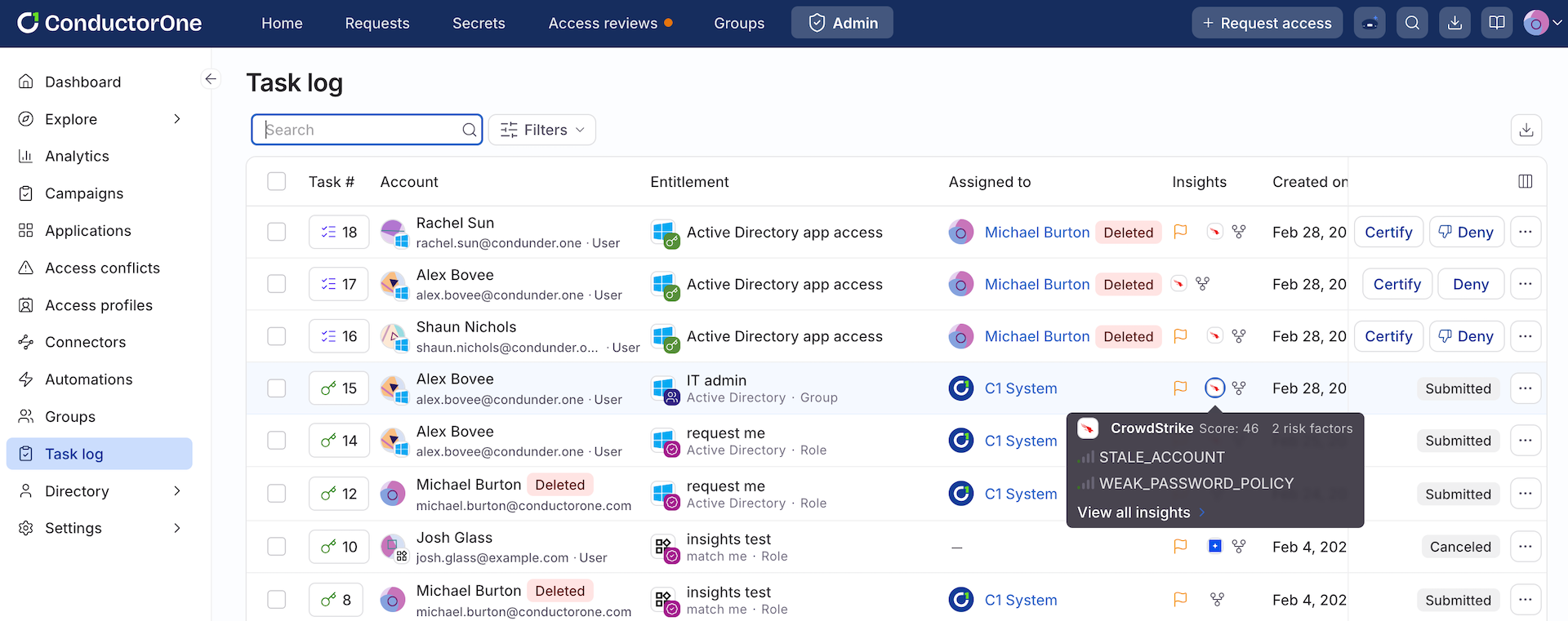
That question now has an answer. C1 just announced a strategic integration with CrowdStrike Falcon® Next-Gen Identity Security. Falcon risk scores now ingest directly into C1 — attached to identities, actionable as conditions in governance policies, and capable of triggering automated access decisions the moment risk changes.
CrowdStrike doesn't just understand endpoints — it understands identity risk. Falcon Next-Gen Identity Security surfaces signals about compromised credentials, anomalous behavior, lateral movement patterns, and identity-based threats as they emerge. These aren't static attributes. They're dynamic indicators of whether an identity can be trusted in a given moment.
C1 is the governance control plane for the agentic enterprise — automating dynamic access controls and always-on governance for every human user, non-human identity (NHI), and AI agent across your environment. This integration makes CrowdStrike's real-time risk intelligence part of that governance layer, continuously. What used to be a static access decision becomes a living system.
How it works: Risk as a condition, not just a label#
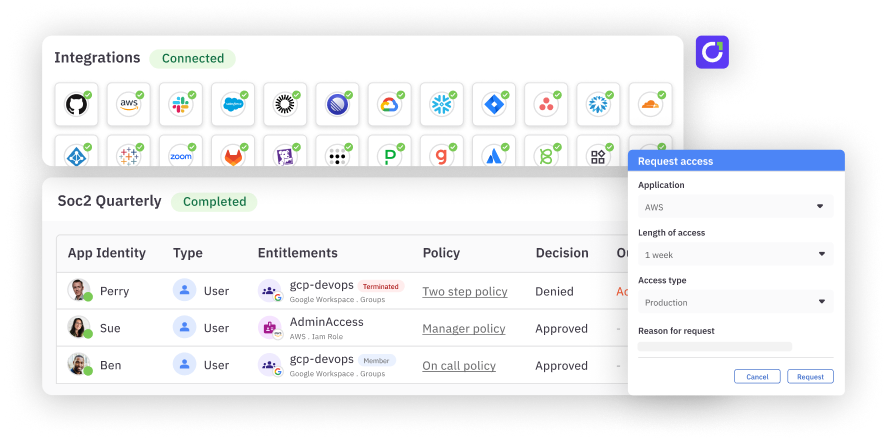
Risk score ingestion is simple to enable through your existing CrowdStrike connector in C1. Once configured, Falcon risk scores and severity levels attach to identities across your environment — human users, service accounts, and AI agents alike.
Visibility is useful. But automation is what changes your security posture at scale.
C1's policy engine lets you build conditions that directly reference Falcon risk scores. The moment an identity's score crosses a threshold you define, governance responds — no manual intervention, no waiting for the next scheduled review. If risk increases due to device posture, credential exposure, or identity-driven threat activity, policies adapt in real time. If an identity no longer meets the conditions under which access was granted, that access doesn't persist. It disappears.
What that looks like in practice:
- Auto-reject access requests from identities above a defined risk threshold
- Add stricter approval requirements for high-risk identities requesting privileged access
- Trigger an access review the moment a user's risk score spikes
- Revoke entitlements automatically when risk crosses a threshold — no ticket required
The same logic applies whether you're governing a human employee, a service account, or an AI agent operating at scale. A compromised credential triggers immediate access changes. A service account exhibiting suspicious behavior gets constrained. An AI agent operating outside expected patterns gets limited before it causes downstream impact. Every identity is evaluated not just on who it is — but on how it's behaving and what risk it carries right now.
Risk signals flow into your access approval and review workflows too. In access request approvals, approvers see each identity's current risk context before they act. In access review campaigns, Falcon risk scores appear inline alongside entitlement data — so reviewers can filter and prioritize high-risk identities rather than working through an undifferentiated queue.
Closing the gap between signal and governance#
For years, governance has been retrospective and compliance-driven — focused on answering the question: Who should have access? In a world where identity is a primary attack surface, that's not enough. What matters now is whether access is safe in this moment.
Falcon Next-Gen Identity Security is a first-class data source for every access decision — from policy evaluation to automated revocation to approval workflows. No custom data pipelines. No complex setup. CrowdStrike detects identity risk. C1 governs access. Together, they turn identity governance from a static layer into a real-time control system — one that continuously enforces least privilege as conditions change, for every human, non-human, and agentic identity in your environment.
Read the docs to get started, or request a demo to see risk-aware governance in action.