Discover and secure non-human identities
No more unknowns—view and manage all your identities in one platform.










Master non-human identities with modern IGA
Get full visibility into AI agents, service accounts, API keys, secrets, and more across your environment.
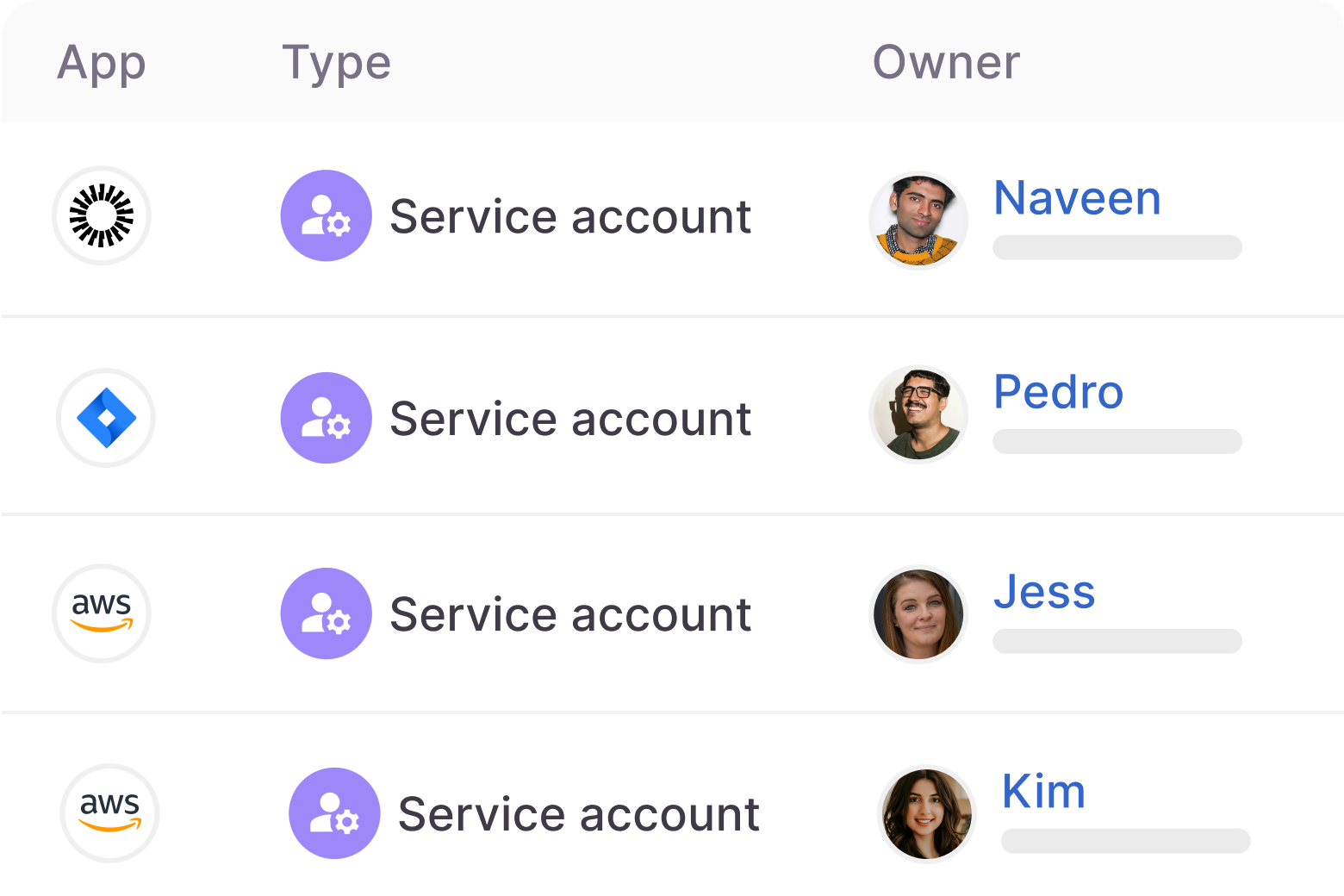
Manage NHI ownership.
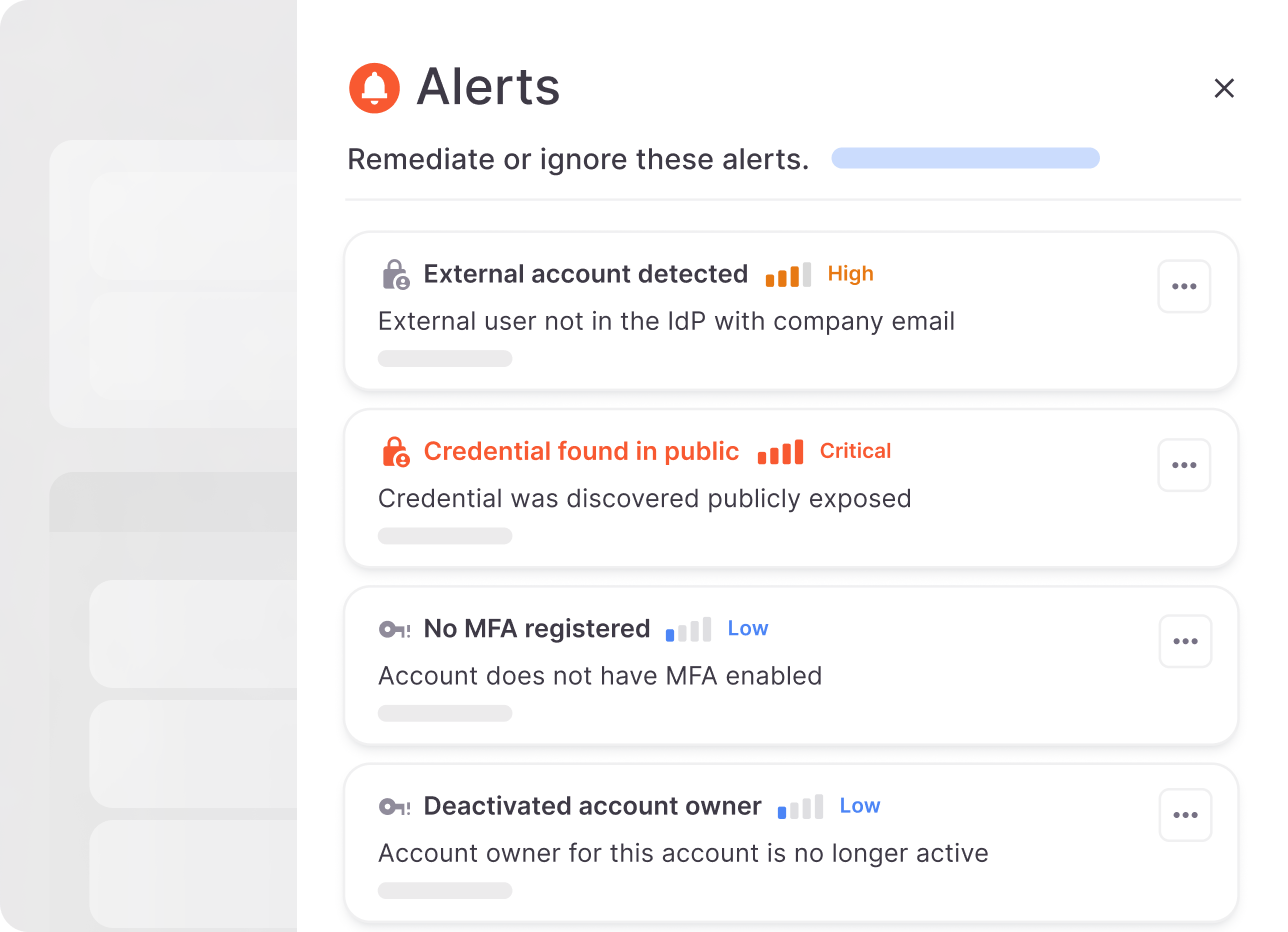
Get alerted to NHI risks.
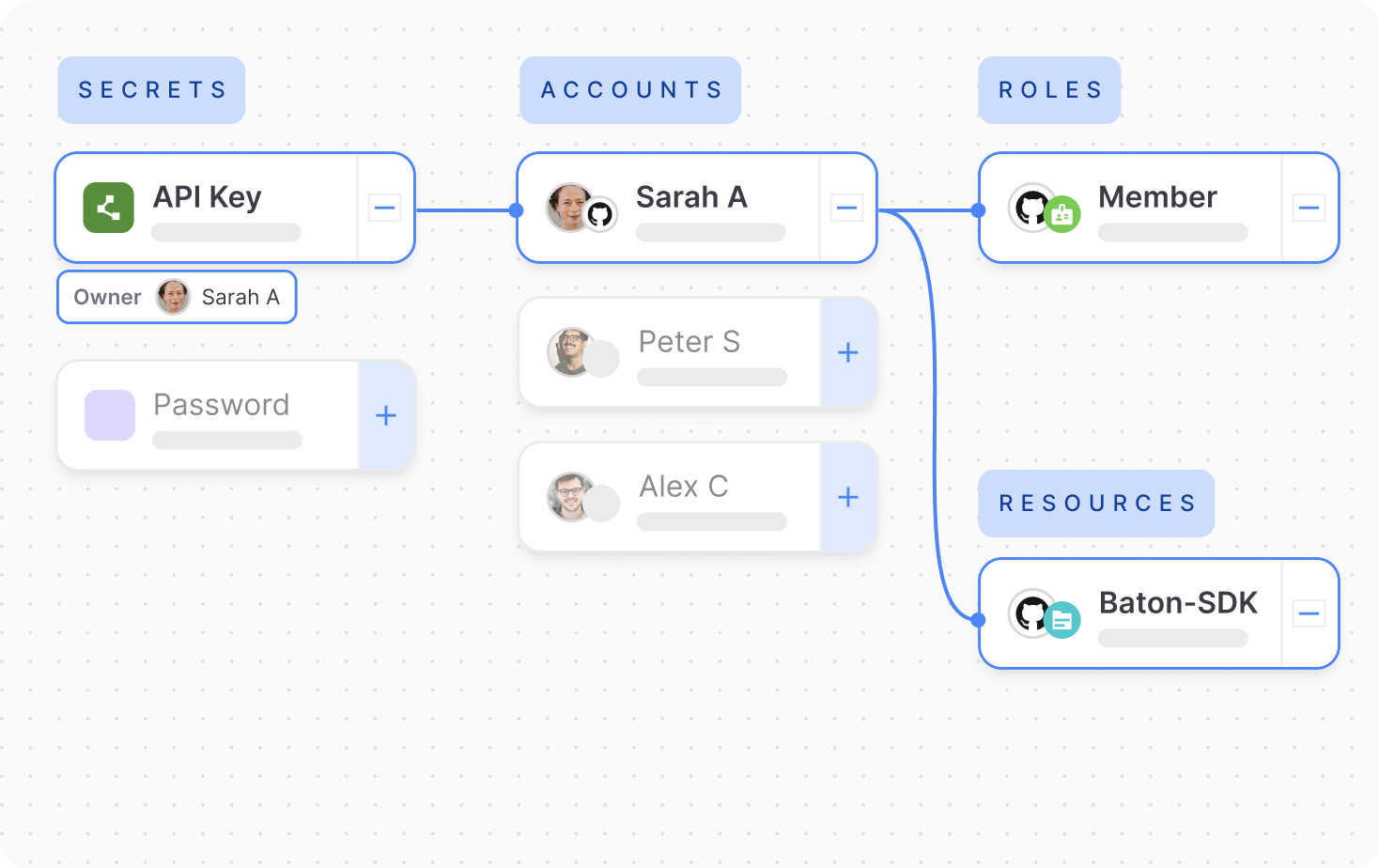
Audit NHI access paths.

“We’ve appreciably improved our security posture without spending a bunch of time and money, which is a huge benefit for our customers.”
Matthew Sullivan, Infrastructure Security Team Leader

How it works
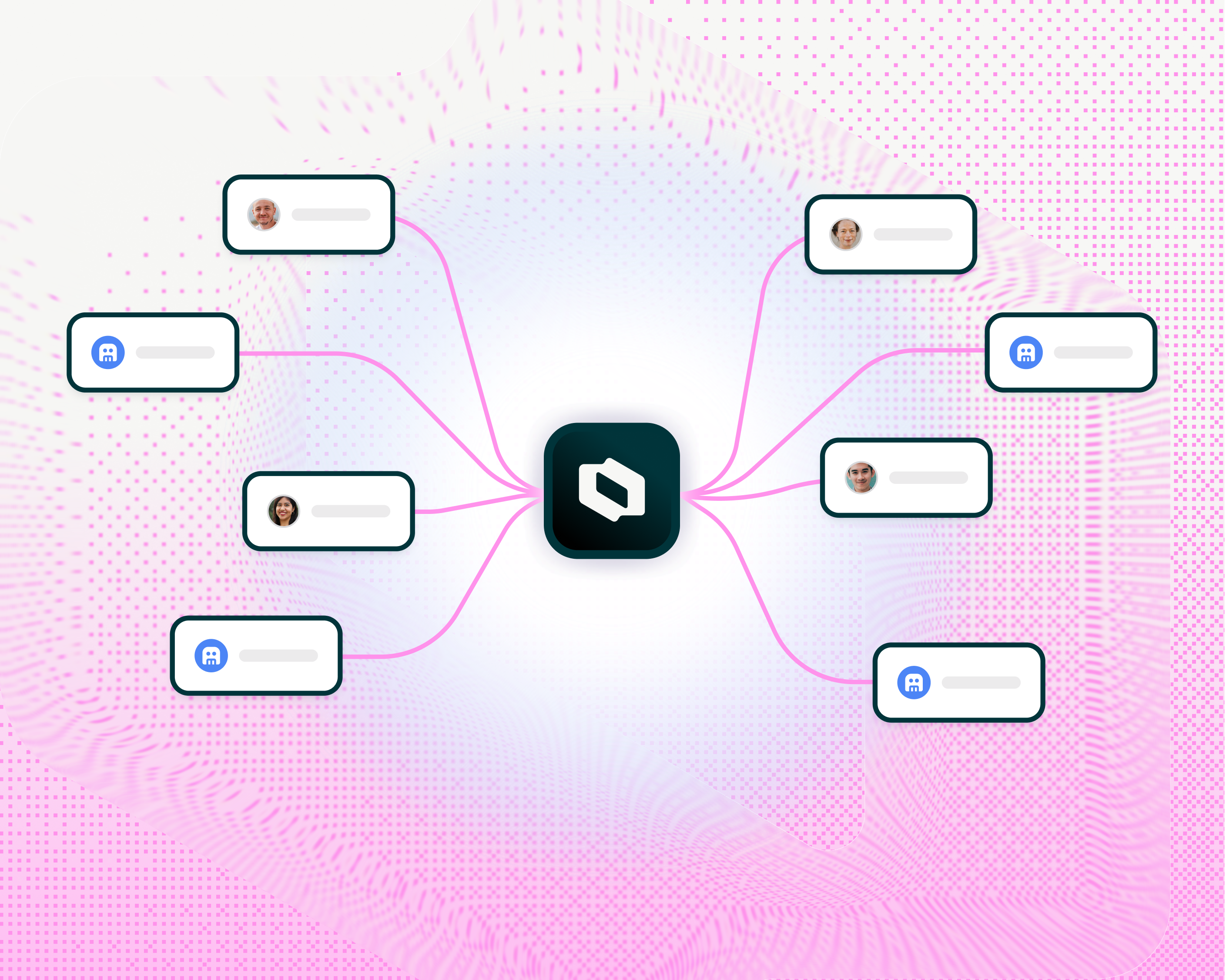
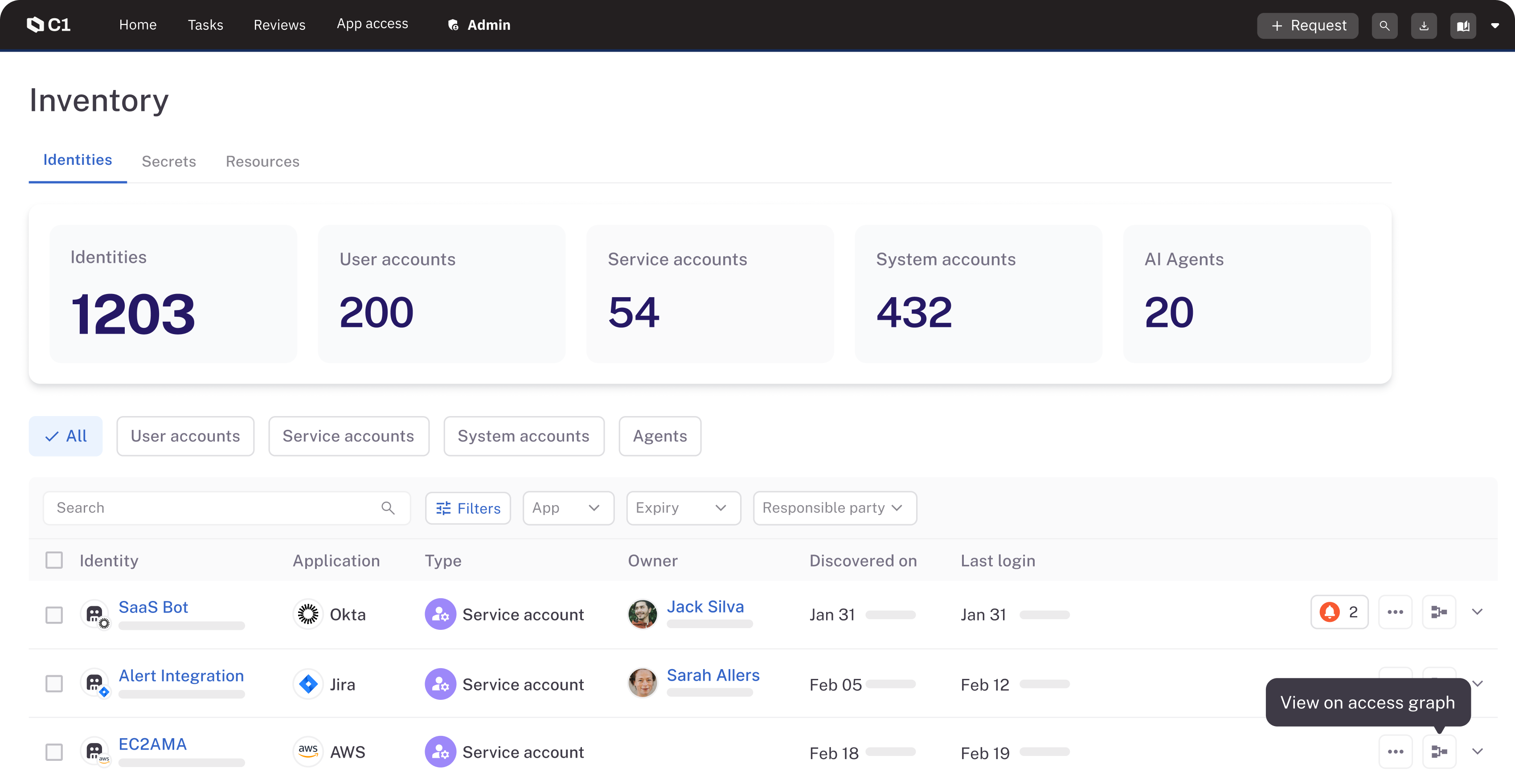
Build your NHI inventory
Lightweight connectors ingest, categorize, and inventory service accounts, keys, tokens, and other NHIs from cloud and on-prem apps.
Apply governance
C1 maps NHI relationships and provides flexible controls for managing the NHI lifecycle.
Identify and remediate risks
Real-time alerting allows you to actively remediate risks like unused API tokens and vulnerable service accounts.
Intuitive, integrated UI
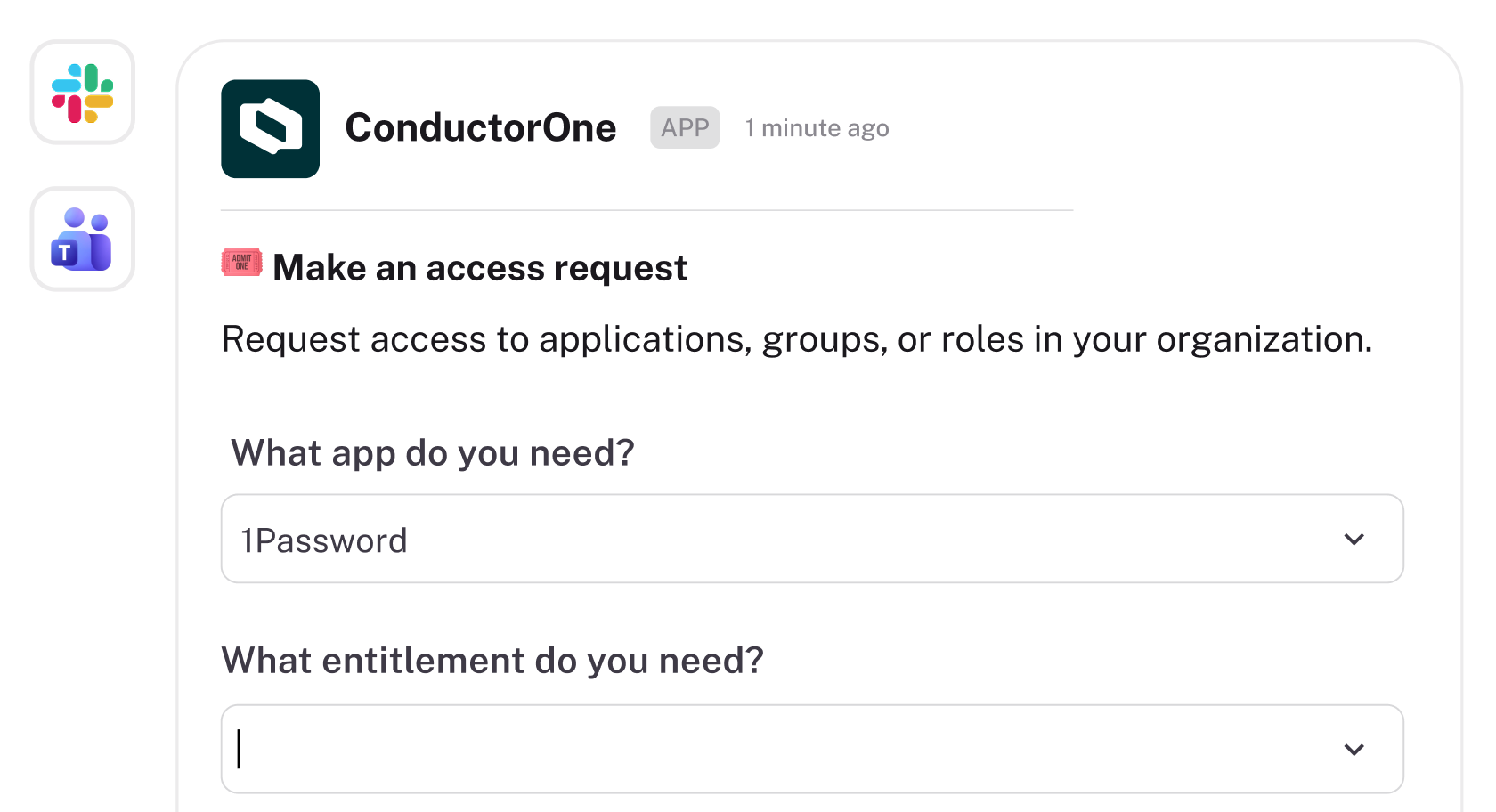
Empower IT, security, and GRC admins as well as end users with a seamless user experience across web app, Slack, MS Teams, and CLI.
One platform to power all your identity use cases

Dynamic Access Controls
Move to contextual, policy-driven access provisioning

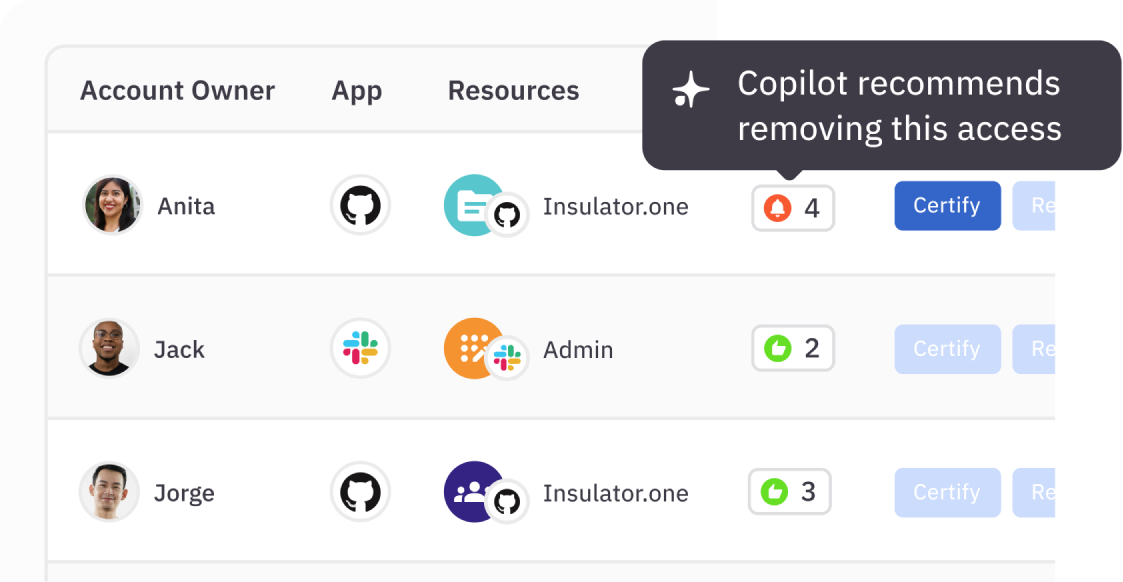
Intelligent Access Reviews
Maintain compliance and improve security without the manual effort

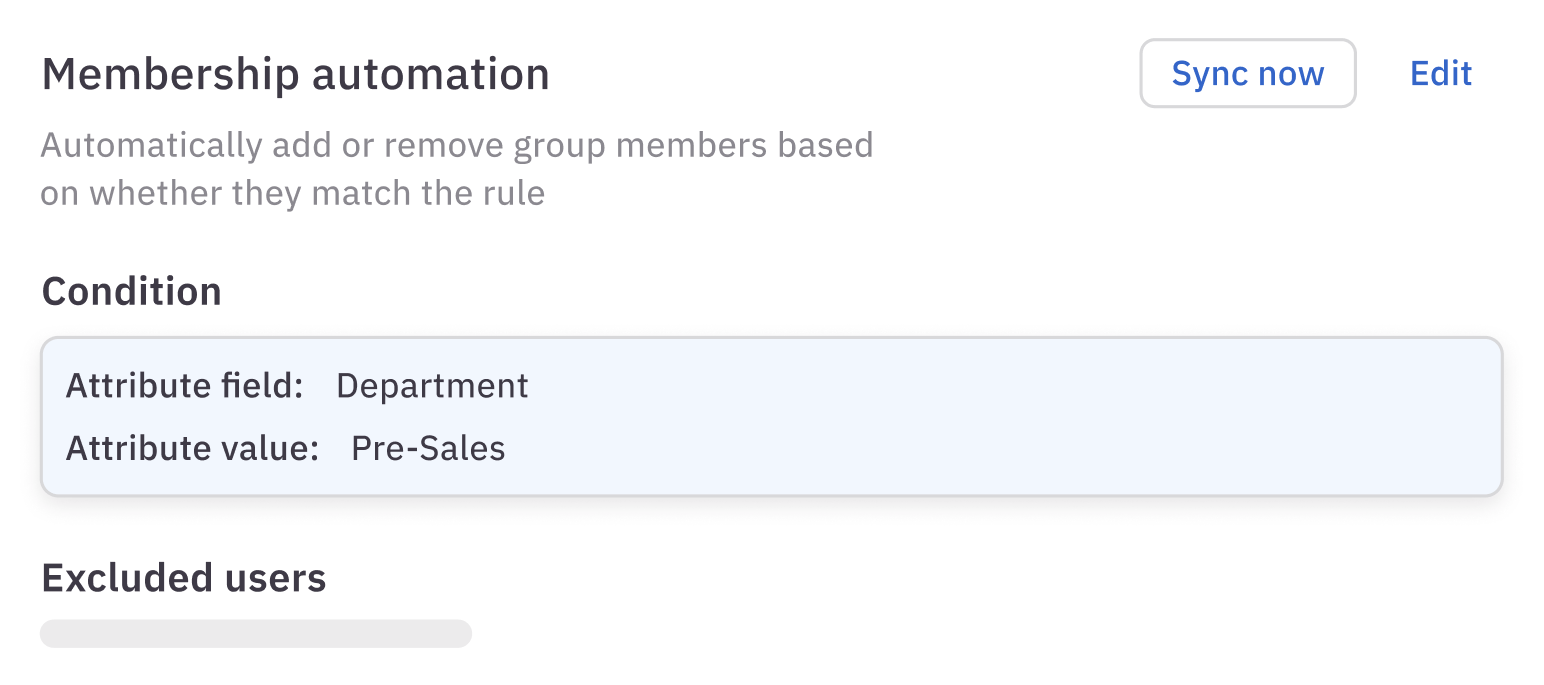
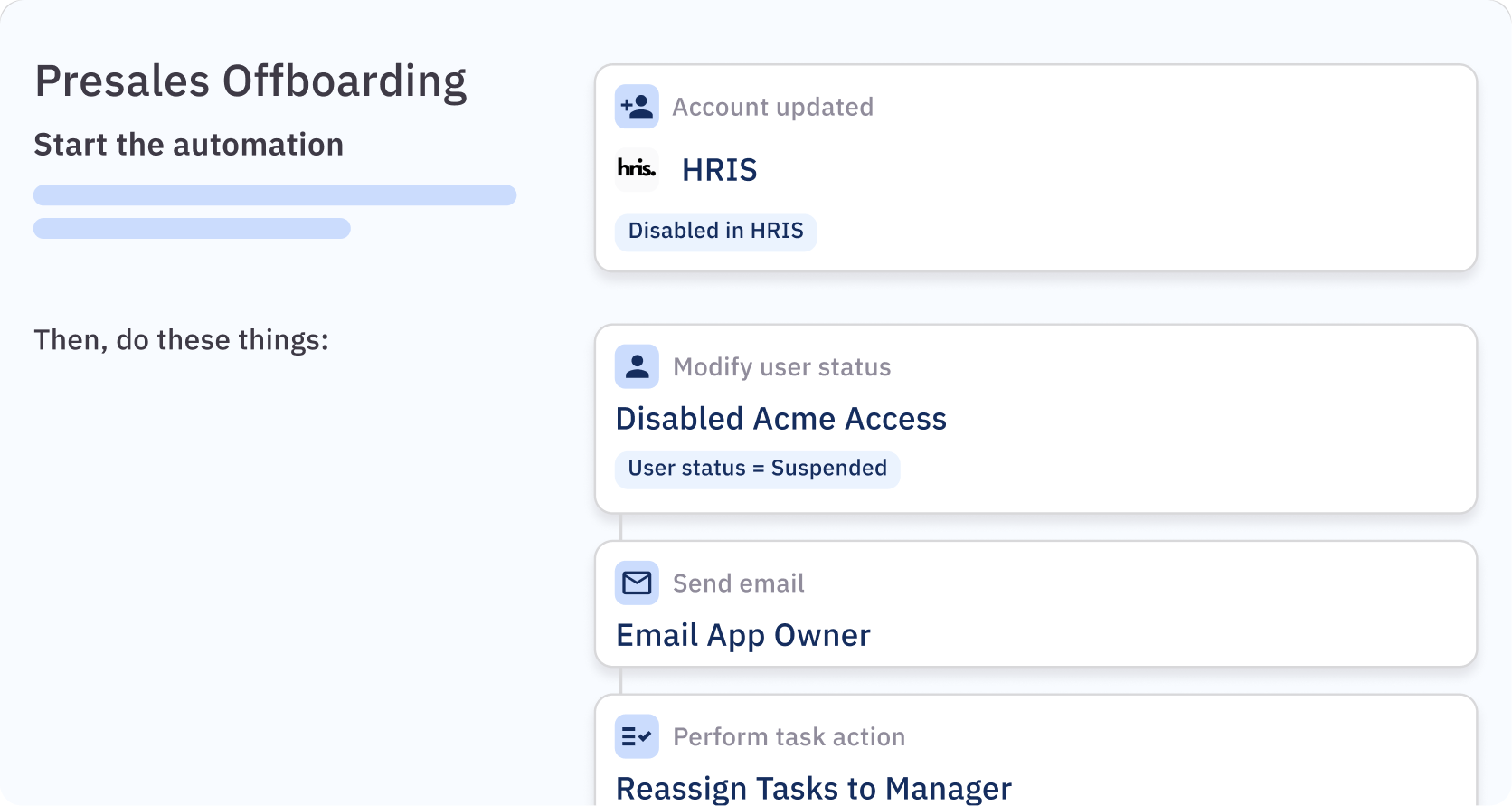
Identity Automations
Build custom identity workflow automations

AI-Native Identity Governance
Manage identity at scale with autonomous AI agents

Latest on the platform

Blog
We Are C1
Today, ConductorOne becomes C1. A new name for a new era of identity — one where AI agents outnumber humans and the identity platform must govern both.