Secure sensitive resources with just-in-time access
Move to zero standing privileges with self-service JIT access to any app, infrastructure, or resource.










Eliminate Standing Privileges with On-Demand Access
Provide frictionless just-in-time access to any resource with self-service requests, smart auto-approval, and no-touch provisioning.
Protect cloud and on-prem infrastructure.
Replace standing privileges with easy-to-request JIT access that’s revoked as soon as it expires.
Simplify compliance.
Fewer standing privileges mean fewer access reviews. Move to JIT access for easier audits.
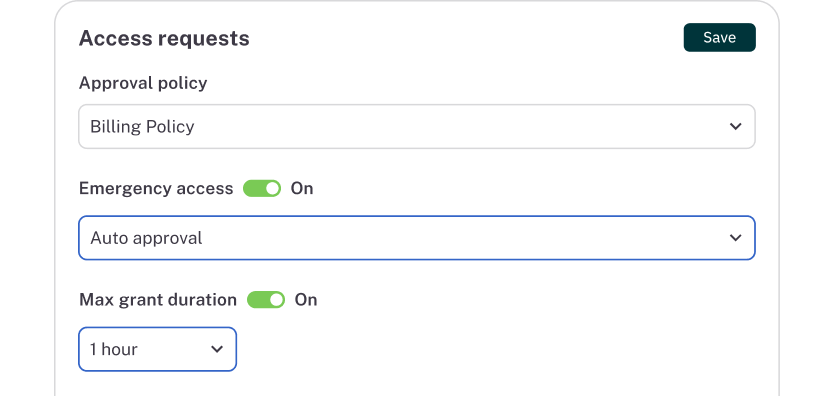
Streamline on-call and emergency access.
Auto-approve JIT access for on-call and break-glass scenarios.

“With just-in-time access, we can greatly reduce our blast radius if something happens.”
Matthew Sullivan, Infrastructure Security Team Leader

How it works
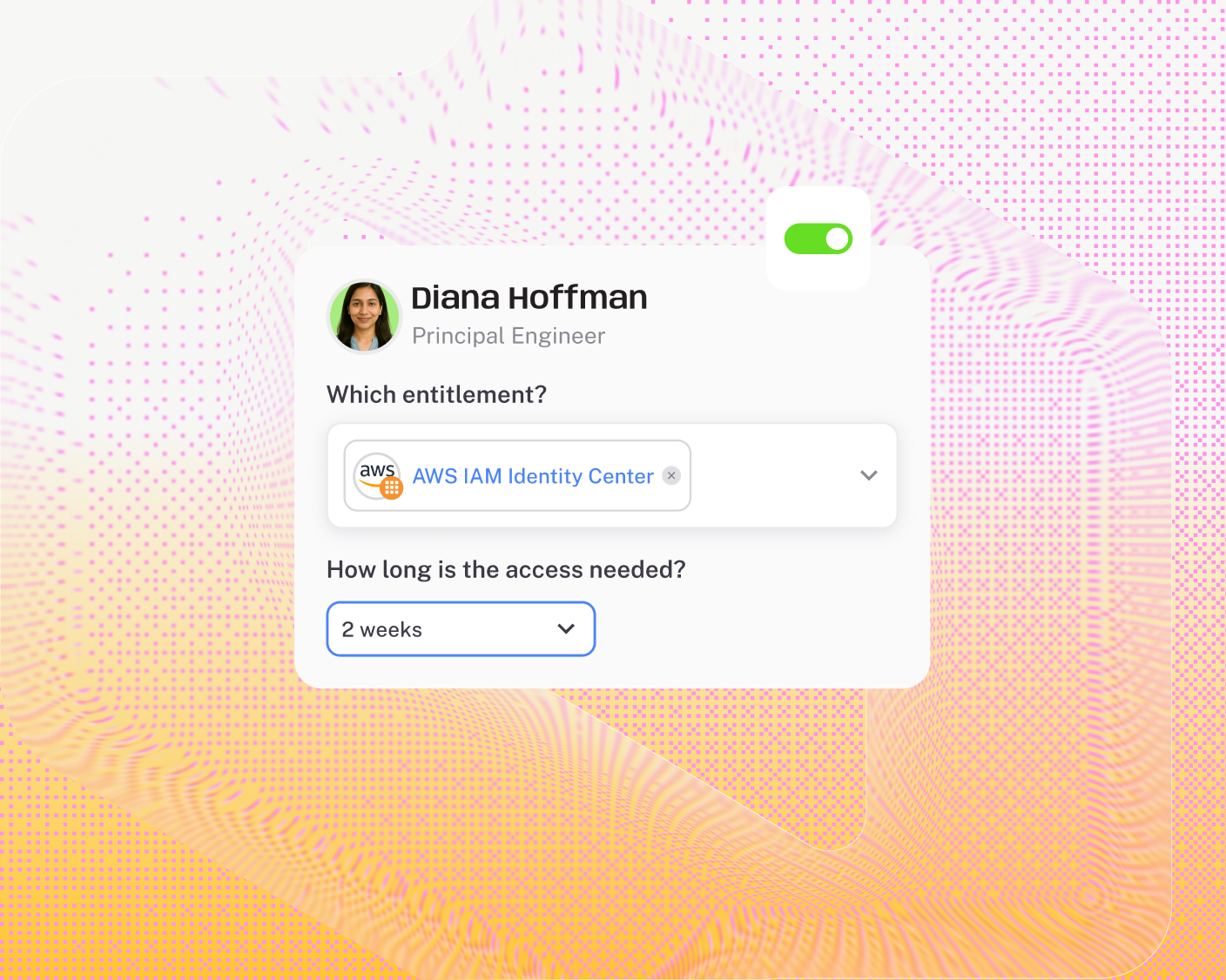
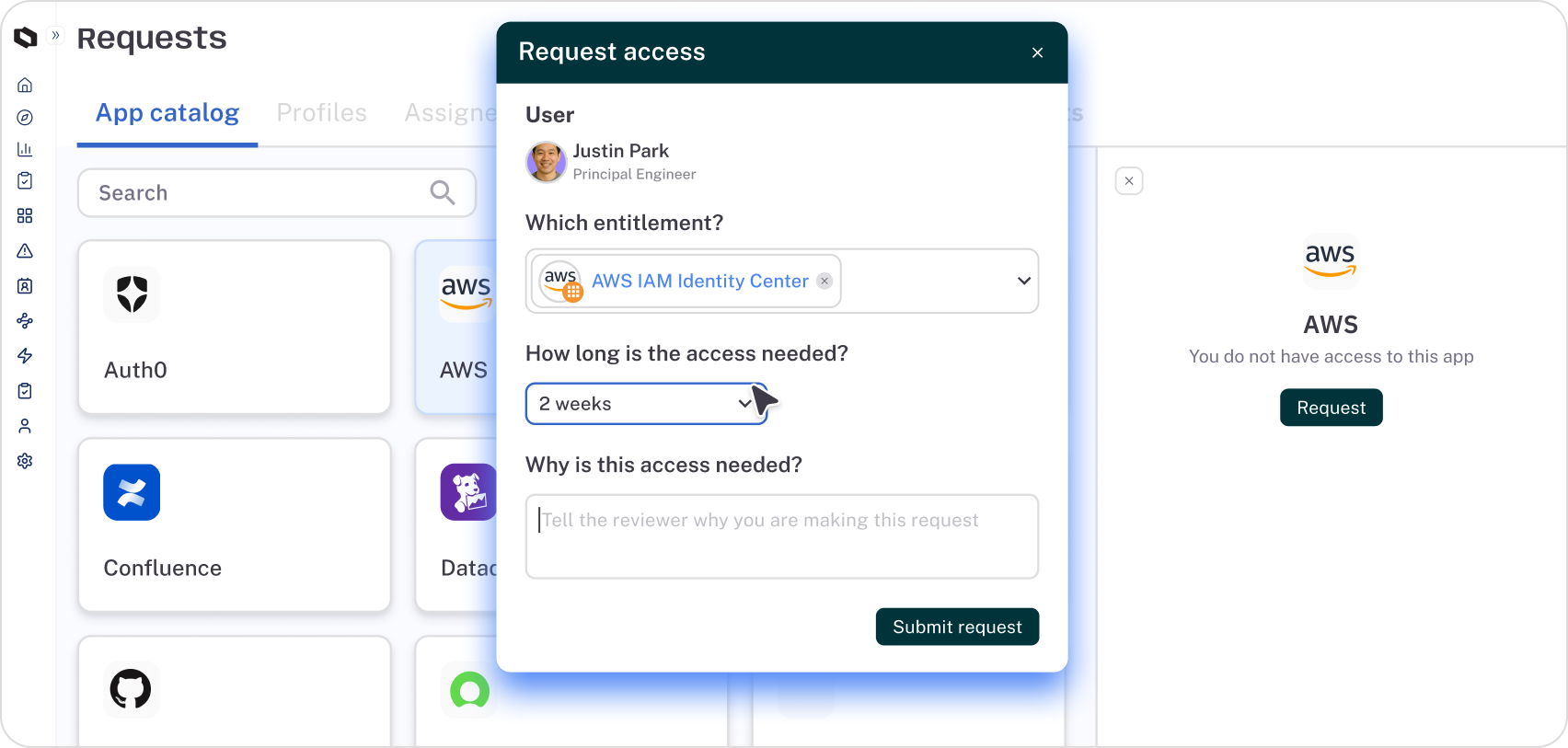
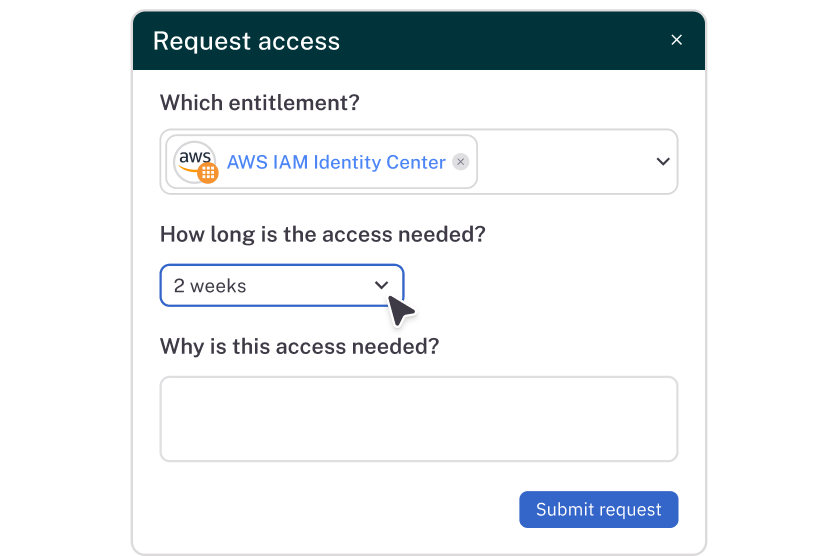
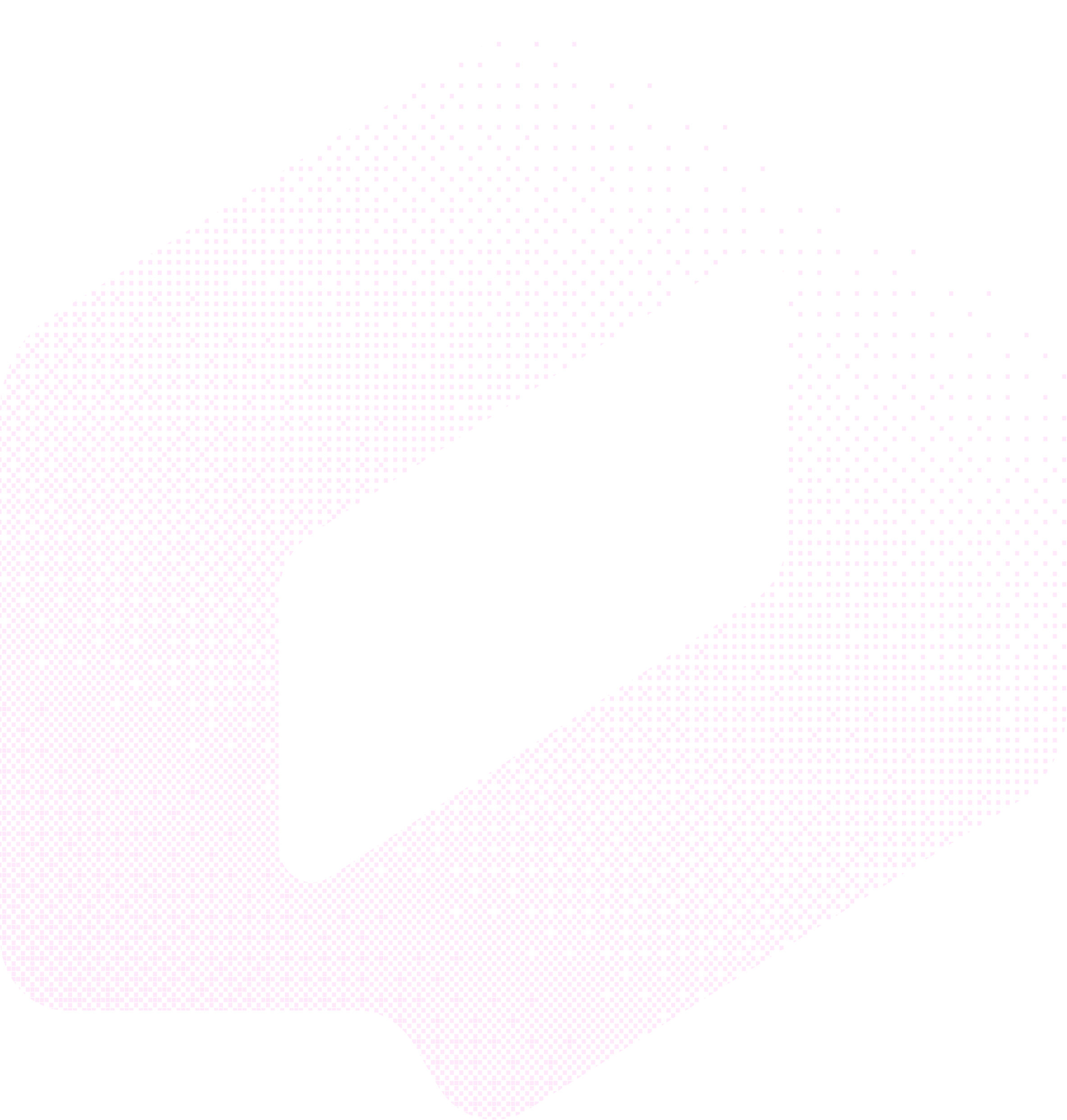
Self-service access requests
Allow users to quickly request JIT access via the web, Slack, MS Teams, or CLI.
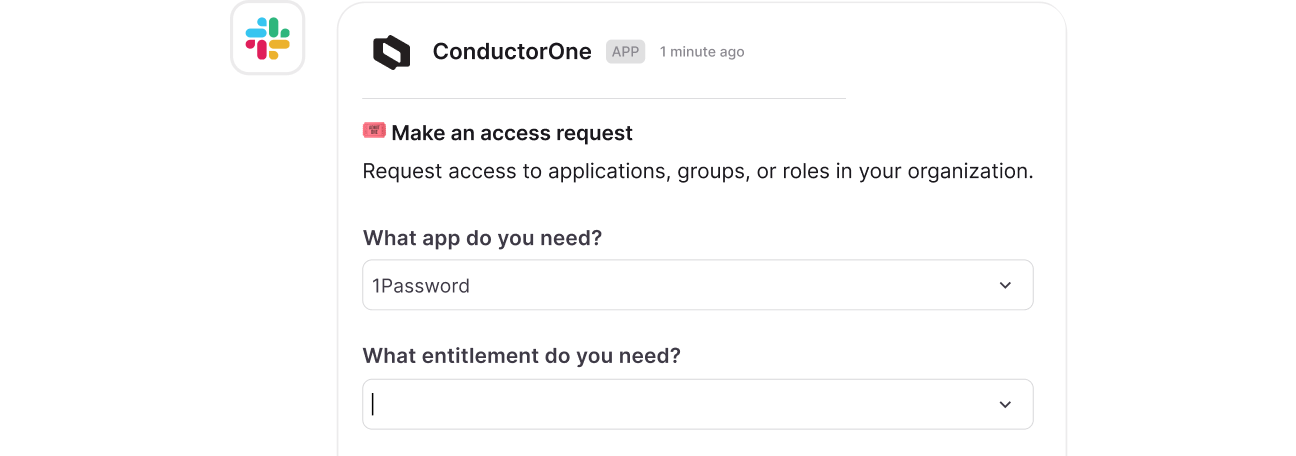
Flexible approval policies
Auto-approve or route JIT requests to the right approvers. Tie approvals to on-call schedules and add security steps like MFA for high-risk access.
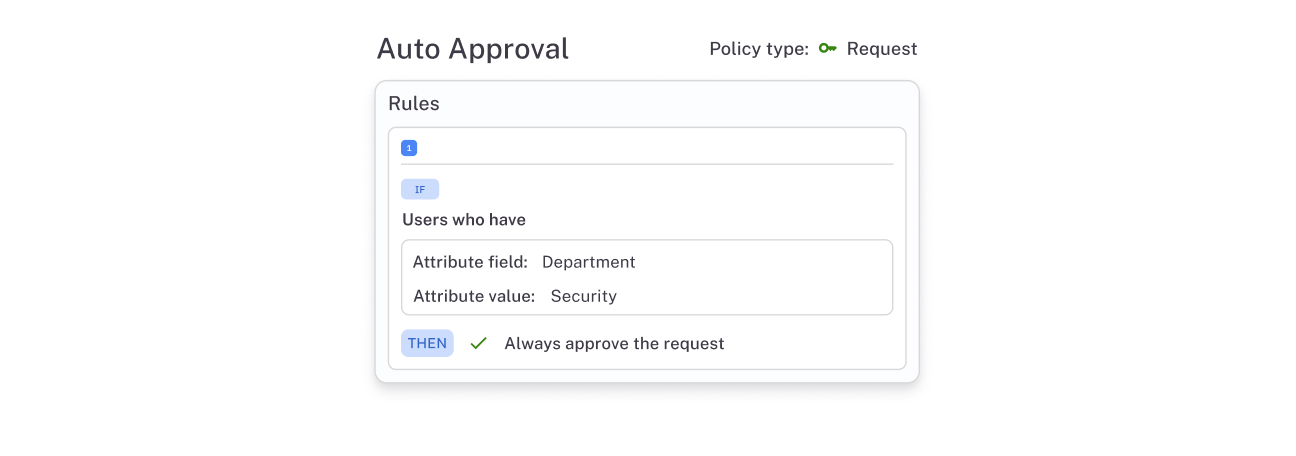
Fine-grained provisioning
Enforce JIT access for any permissions, roles, groups, or resources.
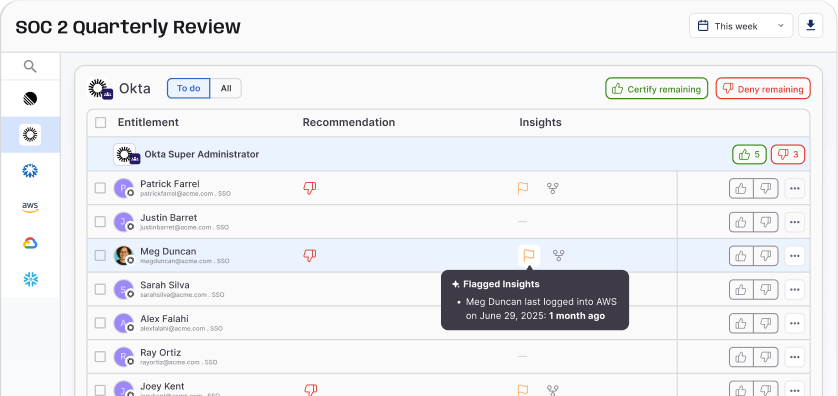
Risk insights for approvers
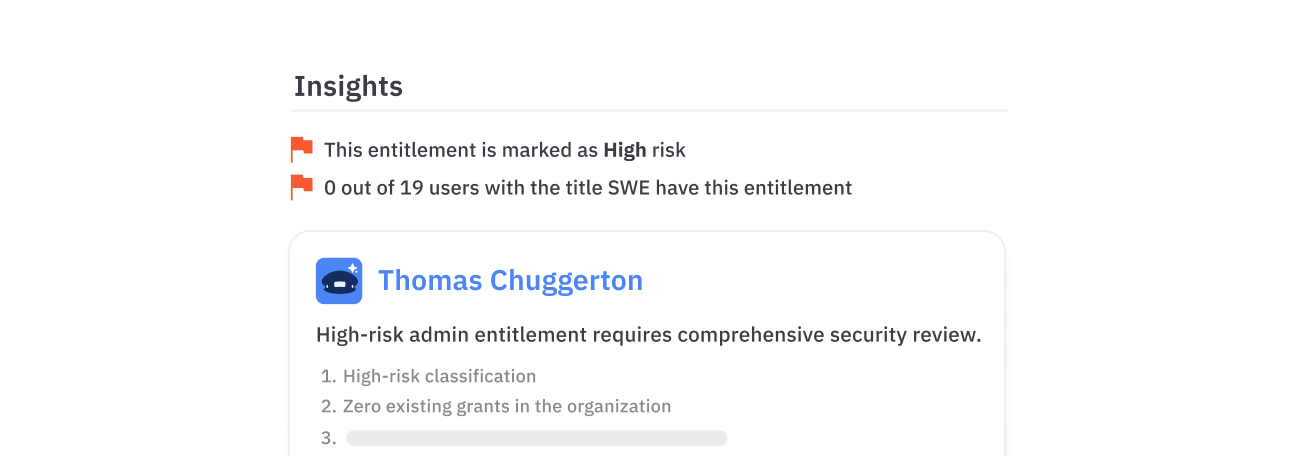
Help approvers make quick, informed access decisions using contextual, risk-based insights.
One platform to power all your identity use cases

Intelligent Access Reviews
Maintain compliance and improve security without the manual effort

Dynamic Access Control
Automate contextual, policy-driven access provisioning

Identity Automations
Build custom identity workflow automations

AI-Native Identity Governance
Manage identity at scale with autonomous AI agents

Latest on the platform

Blog
We Are C1
Today, ConductorOne becomes C1. A new name for a new era of identity — one where AI agents outnumber humans and the identity platform must govern both.