Security at C1
At C1, our team is composed of long-time experts in security, identity, and infrastructure, who have built products from the ground up with highly secure environments.
We understand that our own security and privacy practices are mission-critical to our ability to provide modern privileged access and governance for our customers.
 C1 is SOC2 Type2 certified
C1 is SOC2 Type2 certifiedEmployee Access
Internal systems use SSO and multi-factor authentication whenever possible
Secure password vaults are used for storing credentials when SSO is not supported by a system
Customer API Keys or secrets are not accessible from any internal tooling or dashboards
Background checks are performed annually for all employees
Security training is provided annually for all employees
Network
Employees do not have access to production servers (we only use AWS EKS Managed Node Groups with no remote access)
No workstations have network access to staging or production environments
WiFi in offices provides no additional permissions or authorization grants
Data & Infrastructure
Tenant isolation is ensured through decryption controls within tenant boundaries
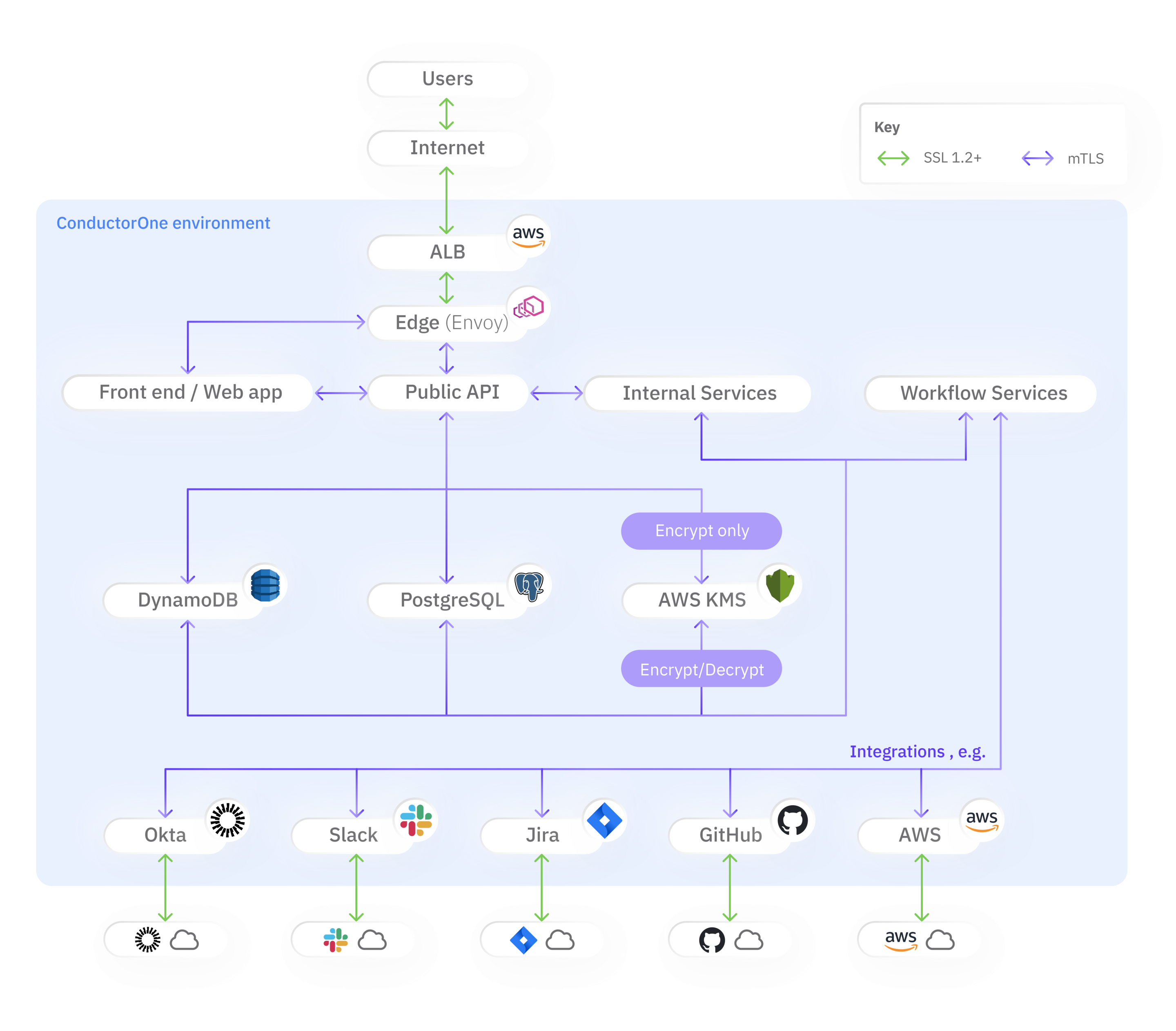
Traffic to C1 is encrypted using TLS 1.2 and greater
API keys and secrets are encrypted with AWS KMS symmetric keys and encrypted again at rest in storage
Internal services and traffic use mutual TLS
Objects are stored and encrypted at rest in AWS DynamoDB
Internet-facing API services are unable to decrypt data
Explicit firewall rules govern all service communications
Services employ highly specific security groups, managed in code
Service Availability
Our infrastructure is deployed across multiple availability zones (US West2 and US East2)
Disaster recovery dry-runs performed annually
Data in our object store (DynamoDB) is backed up continuously
Data is replicated across AWS regions
High Level Architecture
Vulnerability Reporting
We deeply appreciate any effort to discover and coordinate the disclosure of security vulnerabilities. C1 does not currently operate a public bug bounty program or offer monetary rewards for vulnerability reports, but individuals may be acknowledged in a wall of champions.
To support a timely and effective response to your report, please include any of the following:
- Steps to reproduce or proof-of-concept
- Any relevant tools, including versions used
- Tool output
C1 takes all vulnerability reports very seriously and aims to rapidly respond and verify the vulnerability before taking the necessary steps to address it. After an initial reply to your disclosure, which should be directly after receiving it, we will update you periodically with our response and remediation status.
- HTTPS configuration, including supported TLS versions & ciphersuites
- HTTP headers, for purposes including Strict Transport Security, Content Security Policy, and clickjacking/XSS protection
- DNS records including those related to email (SPF, DKIM, DMARC) and certificate issuance (CAA)
- Web applications that appear to allow users to set excessively long passwords

