Secure identity at scale with custom automations.
Replace manual processes with automated workflows tailored to your business and security needs.











“C1 is extremely customizable, very powerful, and doesn’t make assumptions about how your organization works.”
Matthew Sullivan, Infrastructure Security Team Leader

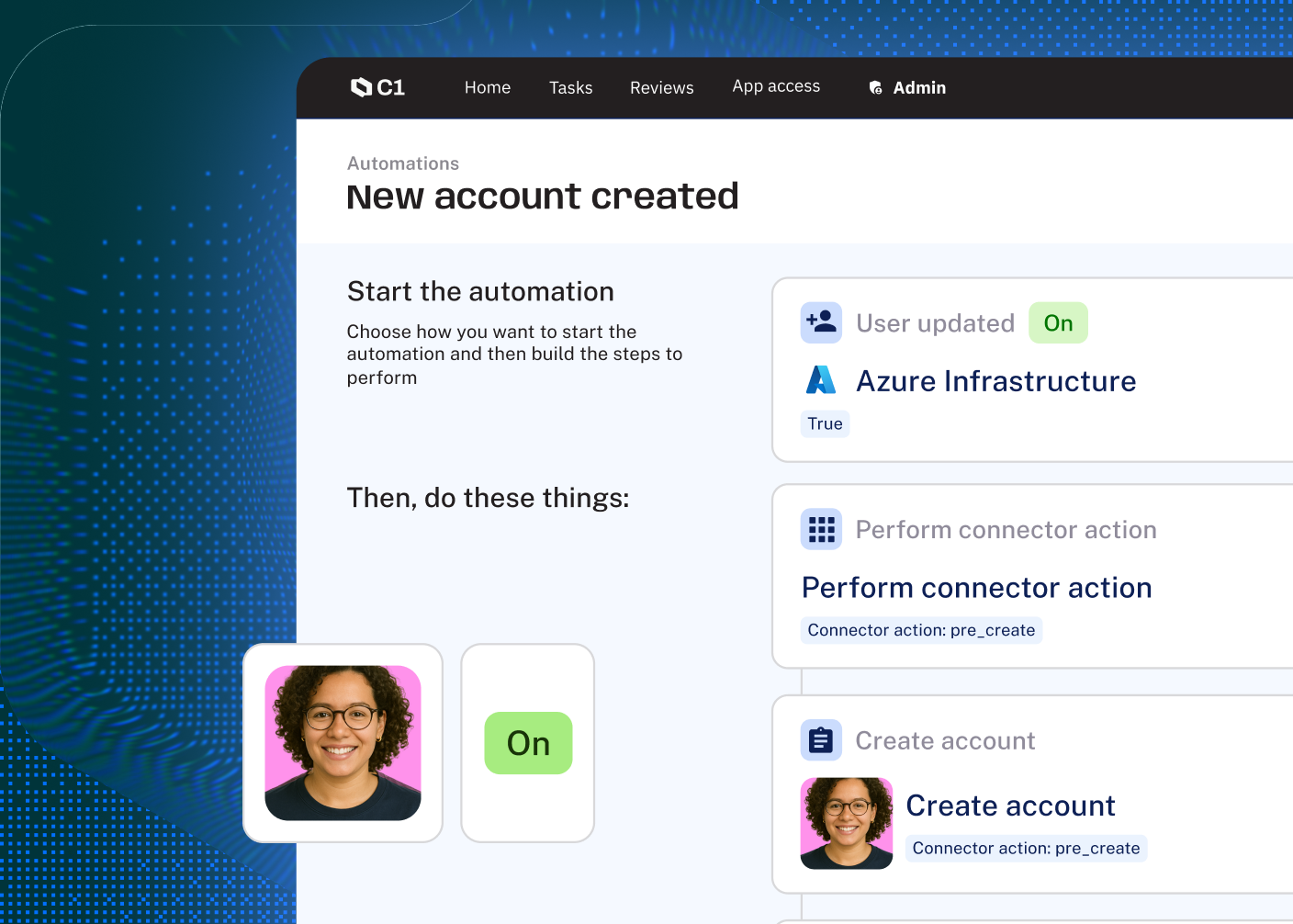
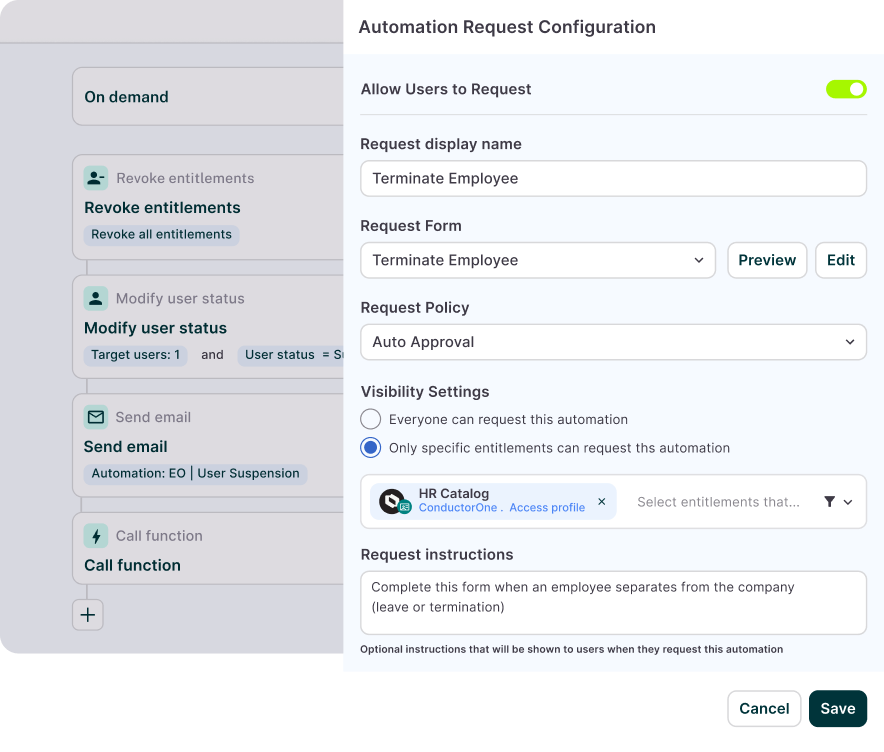
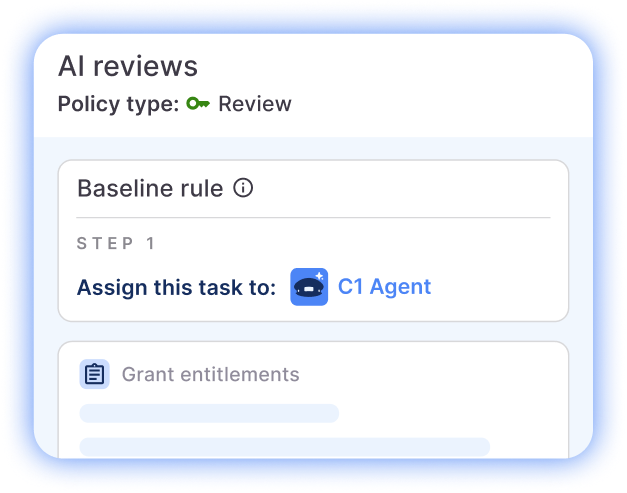
Let AI and users trigger workflows—without privileged access
Empower agents and end users to kick off predefined automations, with approvals and execution handled autonomously. No tickets. No standing privileges. Just frictionless identity operations.
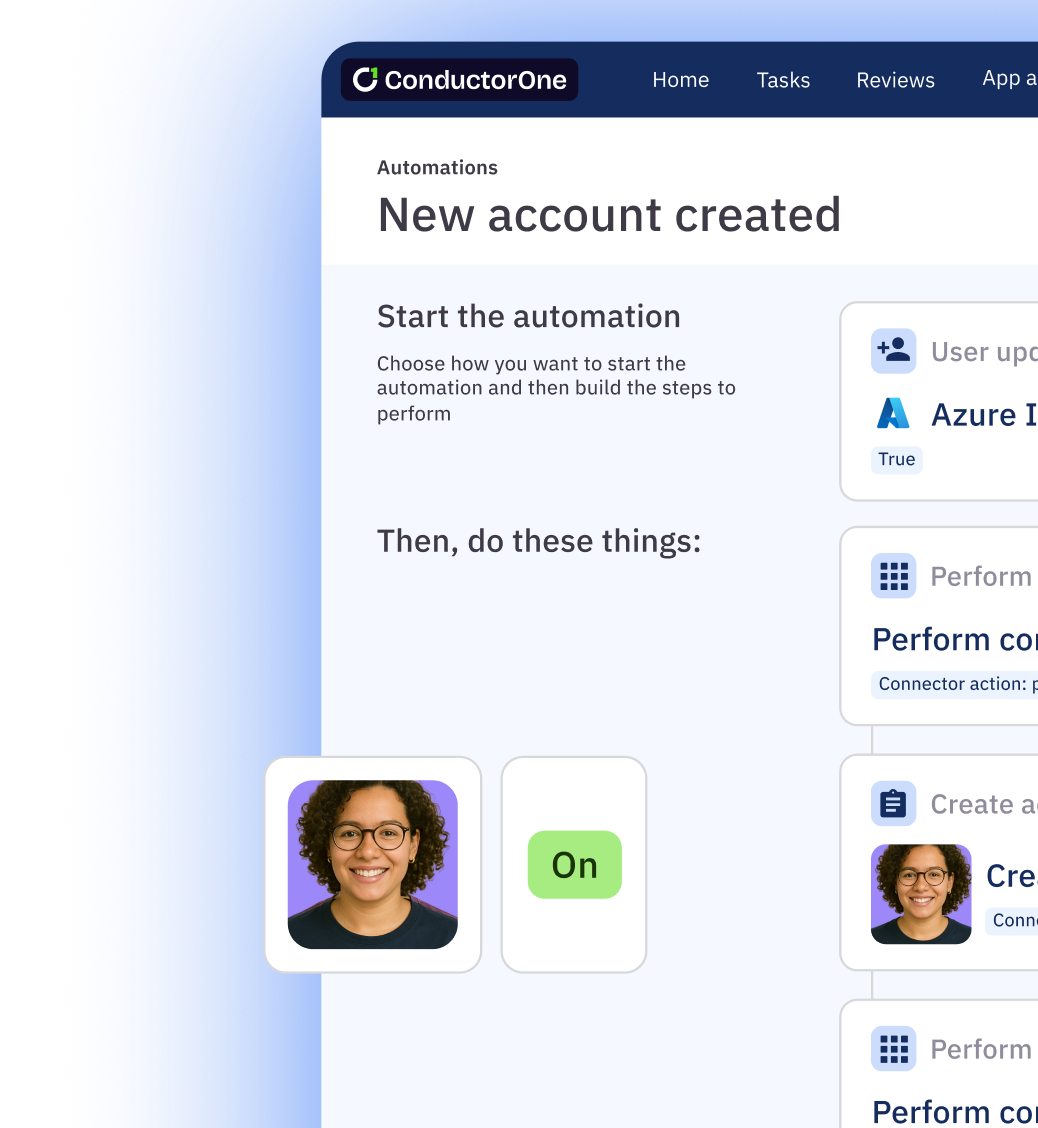
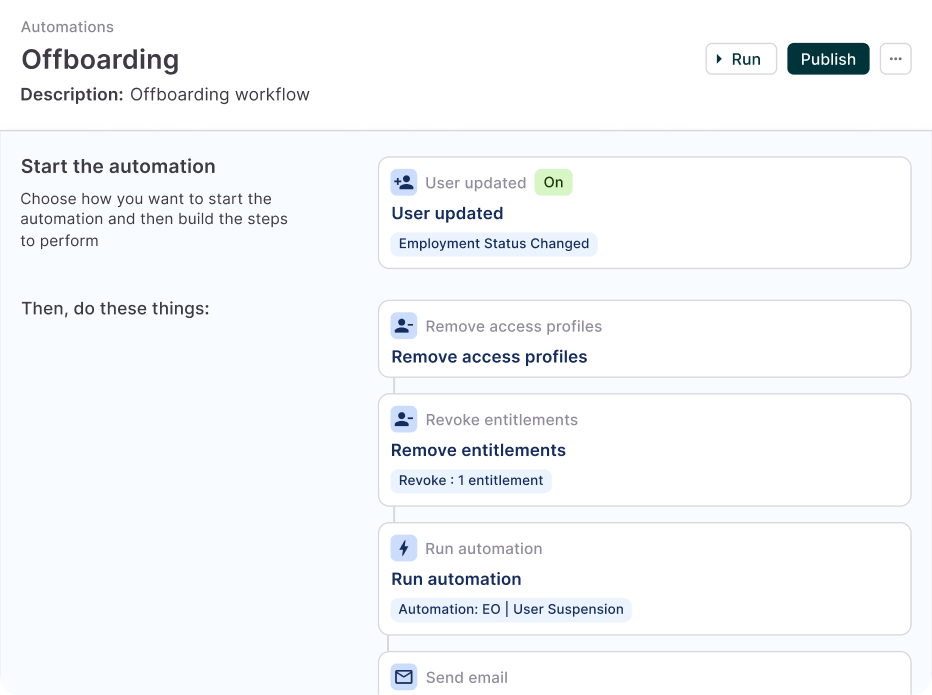
Automate lifecycle management from end to end
Onboard new users in minutes, streamline complex mover scenarios, and ensure swift, thorough offboarding.
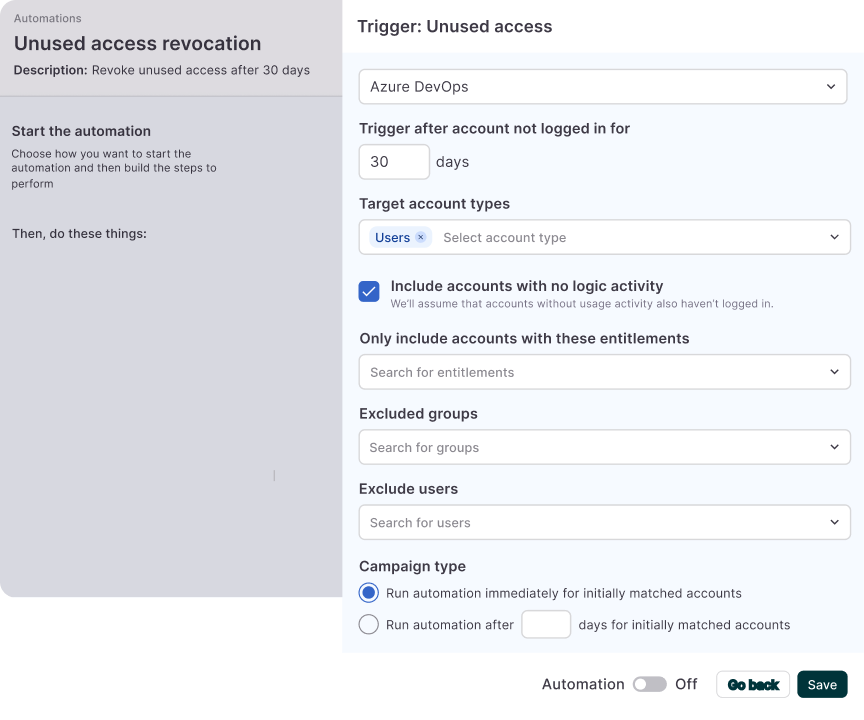
Eliminate unused access
Save on license costs, control permission creep, and securely manage service accounts with detection and remediation of unused access.
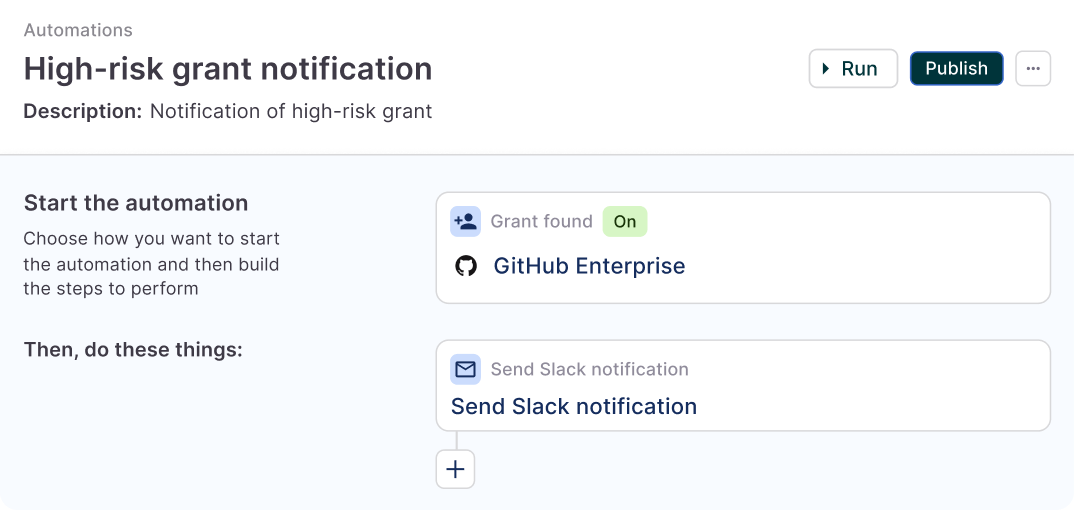
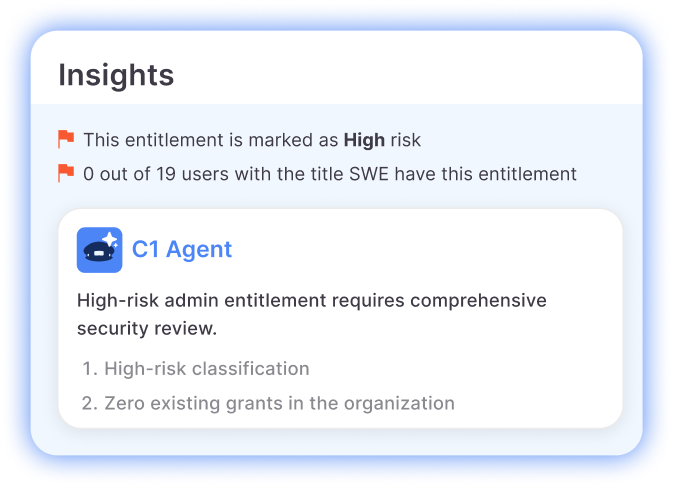
Get alerted to over-permission risks
Discover inappropriate, high-risk, and direct access grants as soon as they occur.
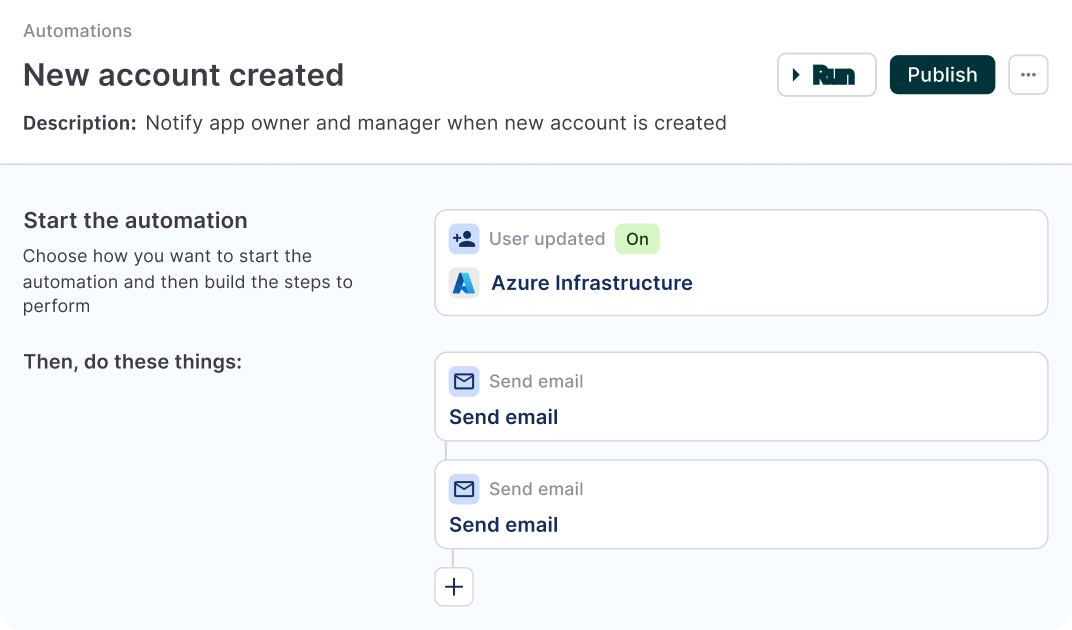
Drive visibility and efficiency
Put stakeholder communications and task reassignments on autopilot to keep everyone informed and processes on track.

Agentic AI + automation = a new era of identity governance
Power all your identity use cases with one AI-native platform

Intelligent Access Reviews
Maintain compliance and improve security without the manual effort

Dynamic Access Control
Automate contextual, policy-driven access provisioning

Just-in-Time Access
Reduce standing privileges with time-bound access

AI-Native Identity Security
Manage identity at scale with autonomous AI agents

Latest on the platform

Blog
We Are C1
Today, ConductorOne becomes C1. A new name for a new era of identity — one where AI agents outnumber humans and the identity platform must govern both.