Comparing Traditional vs AI-Powered IAM Systems
The difference between traditional and AI-based identity and access management (IAM) isn't just a new feature; it's a fundamental architectural and philosophical shift. For years, IAM has been approached as a problem of enforcement, not intelligence.
- Traditional IAM is a reactive, static, and rule-based system. It operates like a set of digital guards with a fixed list of rules, checking permissions only when asked. It’s effective at enforcing what it already knows but is completely blind to novel threats and the nuanced context of modern work.
- AI-based IAM, in contrast, is a proactive, dynamic, and context-aware system. It operates like an intelligent security team, continuously observing behavior, learning what’s normal, and making real-time decisions based on risk and context.
This guide provides a direct comparison of these two models across the core functions of identity management, highlighting the limitations of the traditional approach and the strategic advantages of the AI-powered model.
Traditional vs. AI-powered IAM: a direct comparison#
The architectural differences between traditional and AI-powered IAM are most apparent when you compare how they handle the core functions of identity management. The traditional model is defined by its manual, point-in-time processes, while the AI-powered model is defined by its continuous, data-driven intelligence.
Access reviews and certifications#
The traditional access review process is a manual, periodic chore driven by the audit calendar. An administrator spends days or weeks exporting user access data into spreadsheets, which are then sent to business managers. This process, lacking any real context, famously leads to rubber-stamping**,** where reviewers approve everything just to clear their queue.
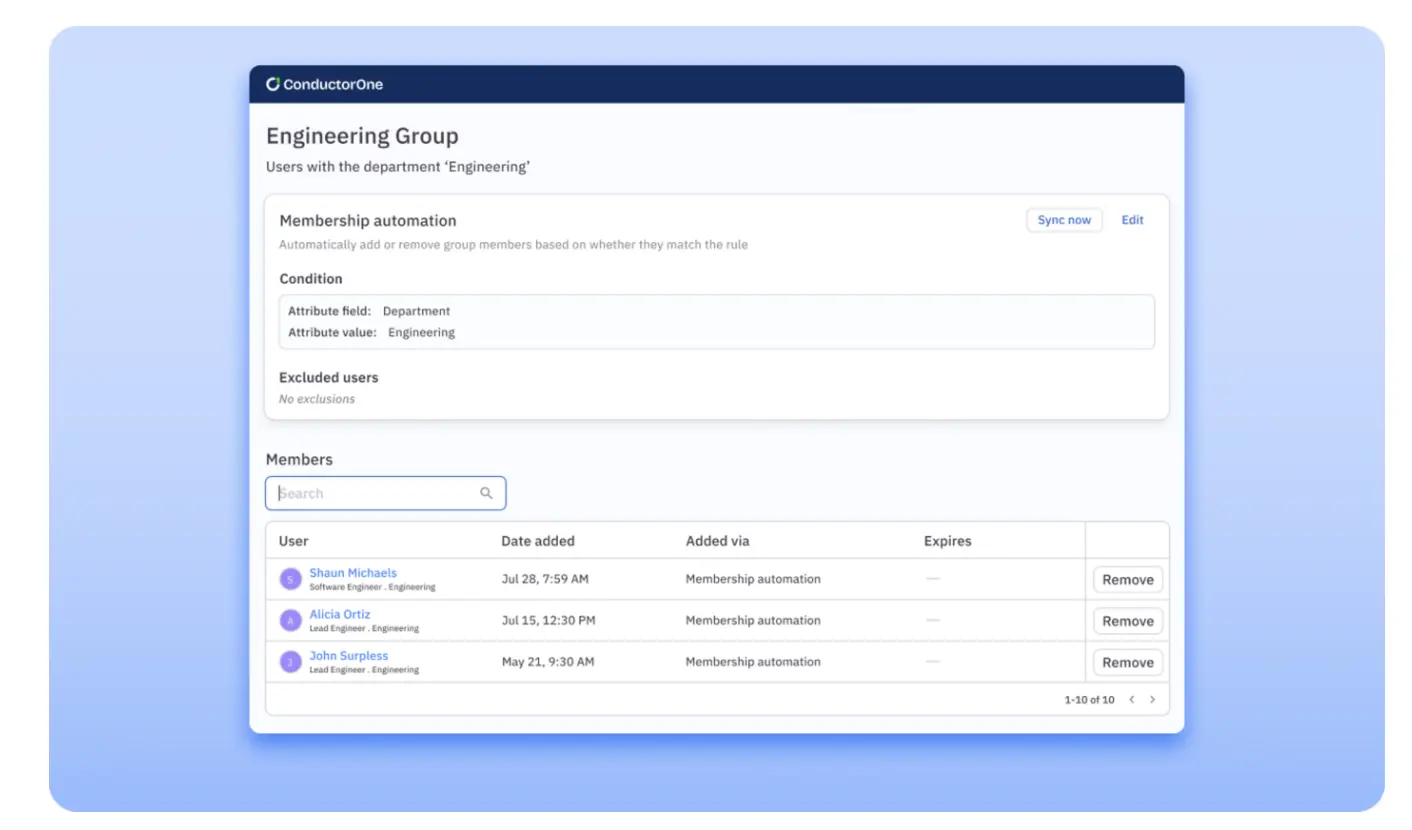
AI transforms this by shifting the process from a point-in-time snapshot to a continuous, intelligent risk-reduction exercise. Instead of just a list of names, an AI-powered platform provides reviewers with powerful, data-driven context.
Instead of a simple spreadsheet, a manager is presented with a clear, prioritized to-do list. For each user, the AI provides a simple recommendation: “Certify - This user's access aligns with their peers and is used daily,” or "Revoke - This user has not used this permission in 180 days.” This transforms the review from a guessing game into an informed decision.
Authentication and access control#
Traditionally, authentication is a static, one-time event that happens at the moment of login. A user presents their credentials, and if they are correct, they are granted access. The critical flaw in this model is that it has no awareness of what happens after the login; a session that was secure at 9:00 AM is still trusted at 3:00 PM, even if the user's behavior becomes suspicious.
AI makes authentication a dynamic and continuous process by assessing the risk of a user's session in the background.
💡Pro tip: This enables adaptive authentication. For a low-risk login from a trusted device, the experience can be seamless and passwordless. If that same user's session later exhibits anomalous behavior—like trying to access a critical system from a new location—the AI can trigger a real-time, step-up authentication challenge or even terminate the session. It applies friction only when the risk warrants it.
Automate birthright and policy-driven access with C1:
✅Provision users on day one with custom access profiles.
✅Auto-adjust access when roles change—no more permission creep.
✅Immediately revoke unneeded access.
Threat detection and response#
A traditional IAM system detects threats based on pre-defined, static rules, such as “alert if there are more than 5 failed logins in a minute.” This approach is effective at catching known, predictable threats but is completely blind to novel or low-and-slow attacks that don't trigger a specific rule.
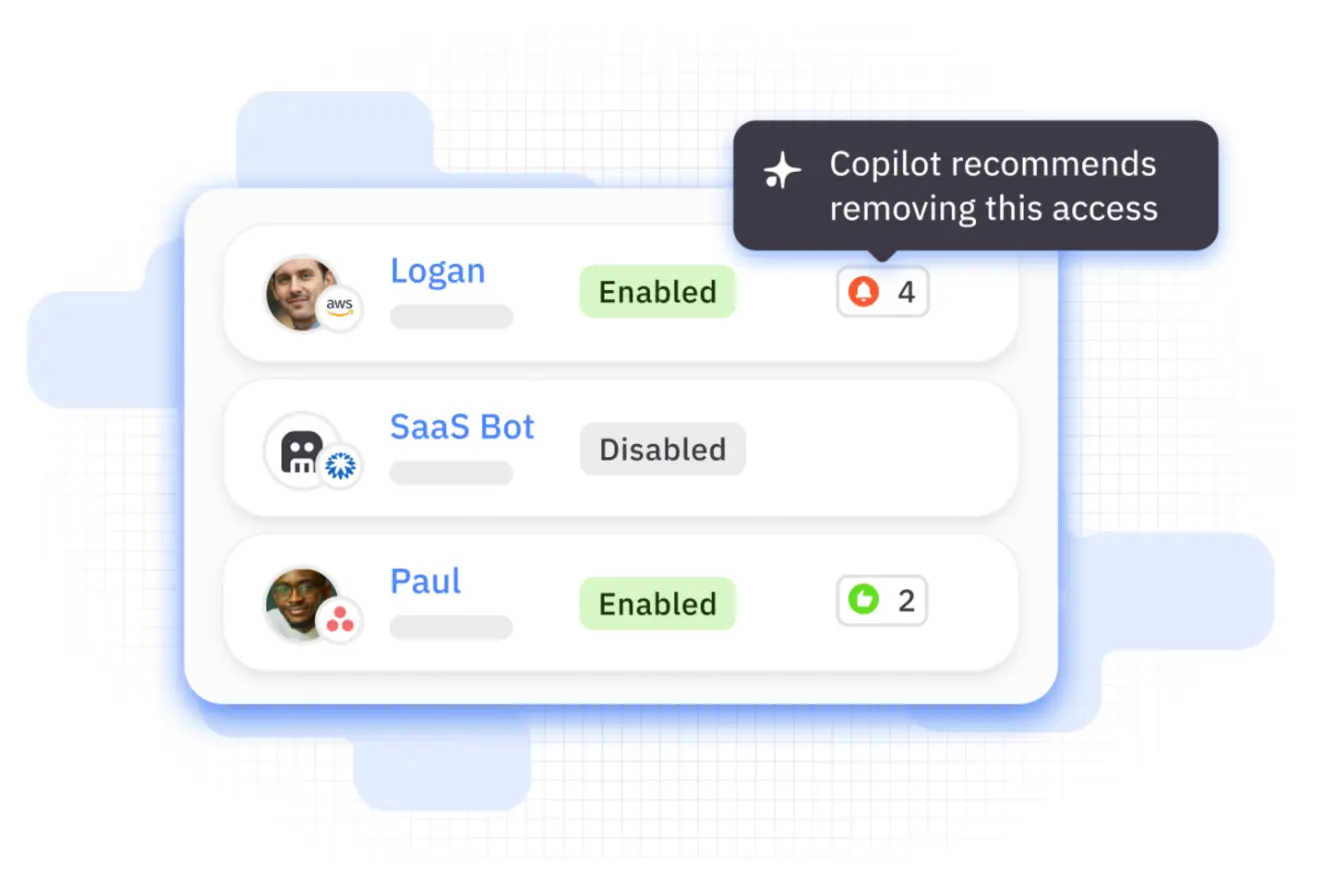
AI shifts threat detection from matching rules to identifying anomalies. It learns a unique baseline of normal behavior for every identity and then flags any significant deviation from that baseline.
This is the only effective way to detect sophisticated insider threats. An AI can flag an employee who, while not breaking any specific rule, suddenly starts accessing files and systems far outside their normal job function—a classic indicator of a malicious insider or a compromised account that a rule-based system would miss.
Policy management and administration#
In a traditional model, policy management is a highly technical and manual task. An administrator must write and maintain complex, code-like rules to define access controls, a process that is slow, requires specialized knowledge, and is a major source of security-related misconfigurations.
AI is moving policy management toward an intent-driven model where an administrator can state their security goal in plain language.
Practical example: An administrator can state, “No user from the sales department should ever have access to the production source code repository,” and the AI will generate the underlying, least-privilege policy. This dramatically reduces the risk of human error and allows security leaders to focus on the strategic what of their security policy, while the AI handles the technical how.
Traditional IAM | AI-Based IAM | |
Model | Reactive and rule-based | Proactive and context-aware |
Access reviews | Manual, periodic snapshot | Continuous, data-driven |
Authentication | Static, at-login check | Dynamic, continuous risk assessment |
Threat detection | Detects known, pre-defined threats | Detects unknown anomalies |
Policy management | Manual, technical, and complex | Intent-driven and conversational |
Primary outcome | Audit compliance | Continuous risk reduction |
Move from a static past to an intelligent future#
The difference between traditional and AI-powered IAM is clear. C1 is the modern, identity governance platform designed to help you leave the limitations of the legacy model behind and embrace a more secure, efficient, and automated future.
We help you make the shift by:
- Transforming your access reviews. Instead of manual spreadsheets, our platform uses AI to provide data-driven recommendations to your reviewers, turning a painful chore into a powerful risk reduction tool.
- Enabling a dynamic, risk-based approach. C1 gives you the real-time visibility and control needed to move beyond static, at-login checks and toward a more intelligent, context-aware security model.
- Automating your security workflows. Our platform is built to automate the core functions of identity management, from lifecycle processes to access requests, freeing up your team from manual, repetitive work.
Stop managing a list of static rules. Start governing a dynamic, intelligent identity program.
To learn more about C1, book a demo.
FAQs:#
Is traditional, rule-based IAM now obsolete?#
Not obsolete, but it is insufficient on its own. Traditional, rule-based IAM is still effective for enforcing well-defined, static policies. However, it is not equipped to handle the complexity and speed of modern threats. The best approach is to use a modern, AI-powered platform that can still enforce your core rules but adds a critical layer of intelligent, adaptive security on top.
What is the first step in moving from a traditional to an AI-based IAM model?#
The most critical first step is to centralize your identity and access data. An AI system is only as good as the data it can see. Before you can leverage AI, you need to implement a modern identity platform that can connect to all your applications and create a single, unified view of all your identities and their permissions.
How do you measure the accuracy of an AI-based system compared to a rule-based one?#
It's a different kind of measurement. A rule-based system is 100% accurate at enforcing its rules, but its scope is very limited. An AI-based system is measured by its ability to correctly identify novel threats while minimizing false positives (flagging legitimate activity as a threat). The goal is not just to be accurate, but to be effective at reducing risk without overwhelming your team with false alerts.
