Users often collect permissions across systems as their responsibilities shift and grow. Most of the time this is harmless. But sometimes those permissions combine in a way that creates real risk. This is where separation of duties (SoD) becomes essential.
At C1 we call these situations access conflicts. They occur when a user holds two or more entitlements that should never be combined. Upholding SoD is a core part of complying with standards such as SOX, FDA 21 CFR Part 11, and ISO 27001.
A classic example is when someone has both accounts receivable and accounts payable. One role allows you to collect money, the other allows you to pay it. Together, they create a potential pathway for fraud, over-provisioning, and serious security or compliance issues.
This is why separation of duties sits at the heart of a strong identity governance program. It is also why we built C1 to prevent, detect, and remediate access conflicts with intelligence and automation.
What is an access conflict?#
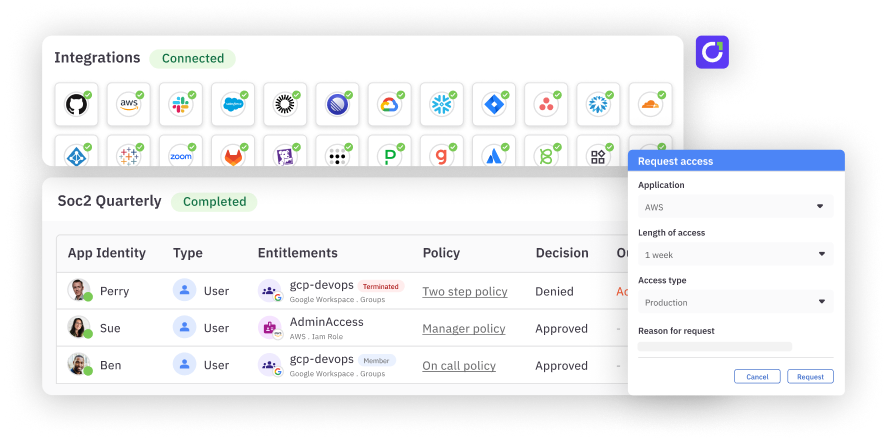
An access conflict happens when a user is granted entitlements from two different groups that should remain mutually exclusive. In C1, you define these groups, and the platform continuously monitors for violations.
If a user has any entitlement from Group A and any entitlement from Group B, C1 identifies the overlap and flags it as a potential conflict.
How C1 prevents conflicts before they happen#
Most legacy IGA tools detect conflicts only after they are already in place. C1 takes a more powerful and proactive approach. The platform can surface and block conflicts at request time, inside reviews, or automatically through policies.
1. Real-time conflict detection during access requests#
If a user with accounts receivable requests accounts payable, C1 immediately identifies the potential conflict and displays a flagged insight on the task details page. Approvers see the issue instantly and can make an informed decision instead of blindly approving.
This helps teams avoid accidental conflicts and keeps security reviewers from missing important context.
2. Intelligent, policy-based approval flows#
C1’s policy engine lets you define what should happen when a request might introduce risk.
For example:
- If no conflict exists, follow the standard approval path.
- If a conflict is detected, escalate the request to a manager, the finance lead, or another high trust approver.
Instead of enforcing separation of duties manually or relying on spreadsheets, teams can automate the decision logic in a structured, auditable way.
How C1 detects and remediates existing conflicts#
Even with proactive controls, existing systems may already contain conflicts. C1 makes it simple to continuously monitor and clean these up.
C1’s conflict monitor evaluates access data on a regular schedule:
- Default frequency: C1 syncs conflict data once an hour.
- On-demand sync: If you need faster results, you can use the More Actions menu on the conflict monitor to trigger a manual sync at any time.
This ensures you always have an up-to-date picture of SoD violations across your environment.
You can:
- Detect conflicts through insights
- Run an access review to investigate and validate each case
- Automatically revoke high-risk entitlements using C1 Automations
This gives identity teams a full end-to-end workflow: prevention, detection, and remediation in one platform.
Keep your organization protected with built-in separation of duties#
Access conflicts are one of the most common sources of hidden risk in growing environments. With manual processes, they are difficult to detect and even harder to prevent. C1 changes that with real-time insights, policy-driven controls, and automated remediation.
To learn more about how to model separation of duties and configure access conflict policies, visit our documentation.